Advantages of AI Infrastructure as a Service for Training and Inference
- By Gcore
- April 30, 2024
- 5 min read
In today’s digital age, the remarkable emergence of artificial intelligence (AI) has transformed technology landscapes. AI Infrastructure as a Service (AIaaS) provides a disruptive option for businesses looking to harness the power of AI without making significant investments in physical infrastructure. This article will talk about the several advantages of AIaaS, including efficient scaling and improved computational capabilities for both training and inference workloads. Learn why AI infrastructure as a service is a vital alternative for businesses looking to fully realize the potential of AI technology.
Understanding AI Infrastructure as a Service (AIaaS)
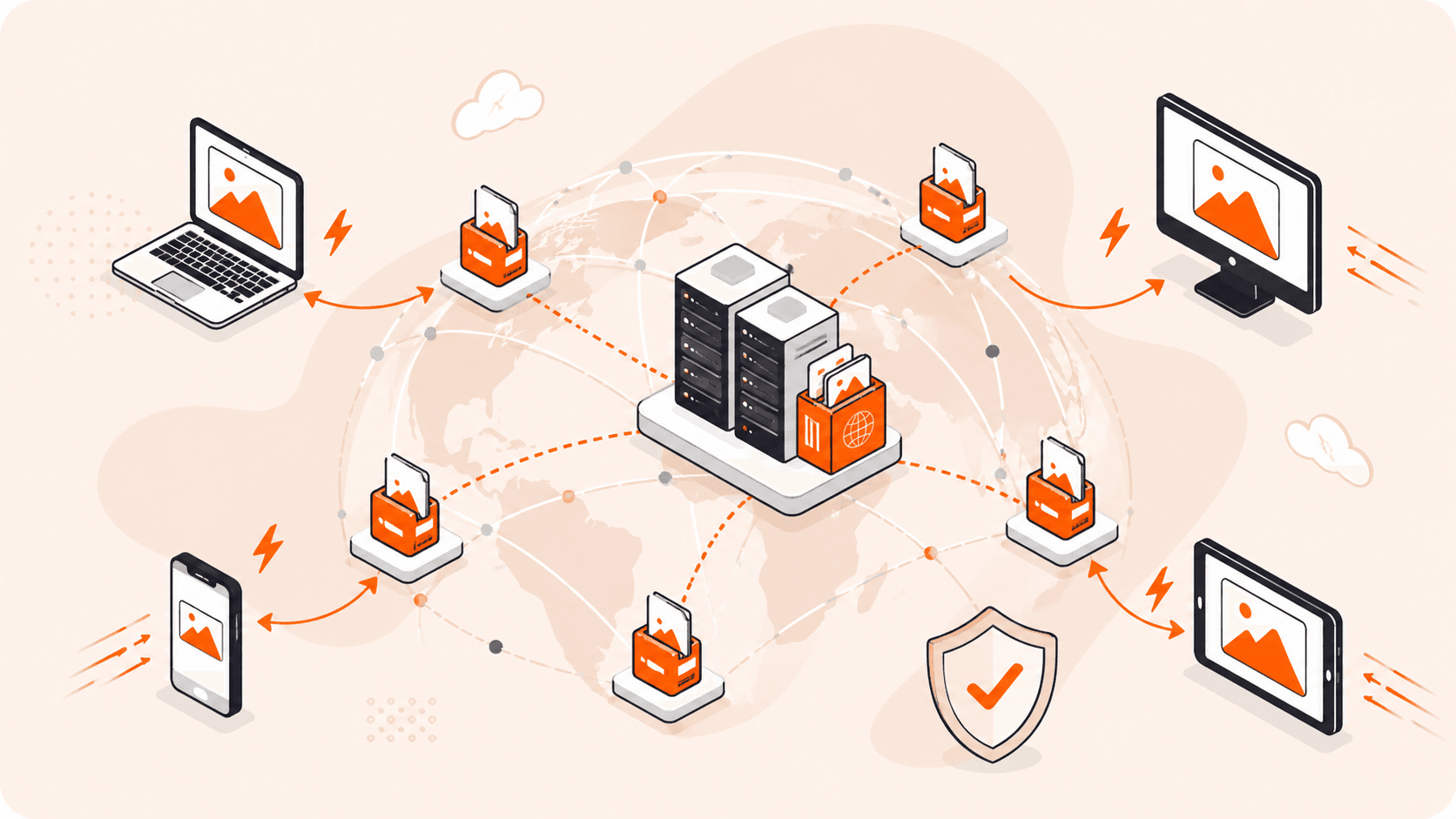
AI Infrastructure as a Service (AIaaS) is a current alternative for organizations and businesses looking to implement AI projects without making a substantial investment and negotiating the complexity of traditional hardware installations. This service model enables you and your company to access, use, and manage AI resources via the internet, thereby outsourcing most of the hard lifting associated with AI implementations.
In the rapidly changing technology ecosystem, AI as a Service (AIaaS) is crucial because it democratizes access to advanced AI capabilities. Small and medium-sized firms, as well as large international corporations, can benefit from cutting-edge AI technologies without incurring significant upfront infrastructure expenses. This accessibility not only encourages innovation, but also allows a broader spectrum of firms to participate in technologically driven marketplaces.
AIaaS fits smoothly into the larger trend of cloud services, reflecting the shift toward more flexible, scalable, and efficient computing solutions.
Key Advantages of Adopting AI Infrastructure as a Service (AIaaS)
Embracing AI Infrastructure as a Service (AIaaS) technology offers numerous appealing benefits that can significantly enhance how firms install and utilize artificial intelligence. AIaaS enables enterprises to streamline operations, reduce expenses, and focus on innovation. In the next section, we will go into the primary advantages of AIaaS, highlighting how it can revolutionize your approach to AI deployment and administration.
#1 Cost Efficiency
One of the most compelling reasons for businesses to embrace AI Infrastructure as a Service (AIaaS) lies in its cost efficiency.
Capital Expenditure Reductions
Traditional infrastructure necessitates large initial investments in hardware and software, which may be a considerable financial burden for enterprises. In contrast, AI Infrastructure as a Service (AIaaS) moves these expenses to the service provider, significantly lowering enterprises capital costs. On-premise data centers also require physical space, which incurs expenditures like construction, rent, and utilities. AIaaS avoids these facility charges by hosting the infrastructure remotely, reducing the financial burden on organizations.
Operational Cost Savings
Maintaining and upgrading on-premise solutions requires continual investments, while AI Infrastructure as a Service (AIaaS) providers handle these aspects, keeping systems up to date at no additional expense to the user. Furthermore, while on-premise systems often require a specialized IT personnel for maintenance and monitoring, AIaaS reduces these IT requirements. This enables organizations to streamline or redirect their human resources, increasing operational efficiency and lowering labor expenses.
#2 Scalability and Flexibility
Apart from cost efficiency, it also offers great scalability and flexibility, making it an ideal alternative for enterprises with changing demand or those who are expanding their operations. Let’s discuss more in the following:
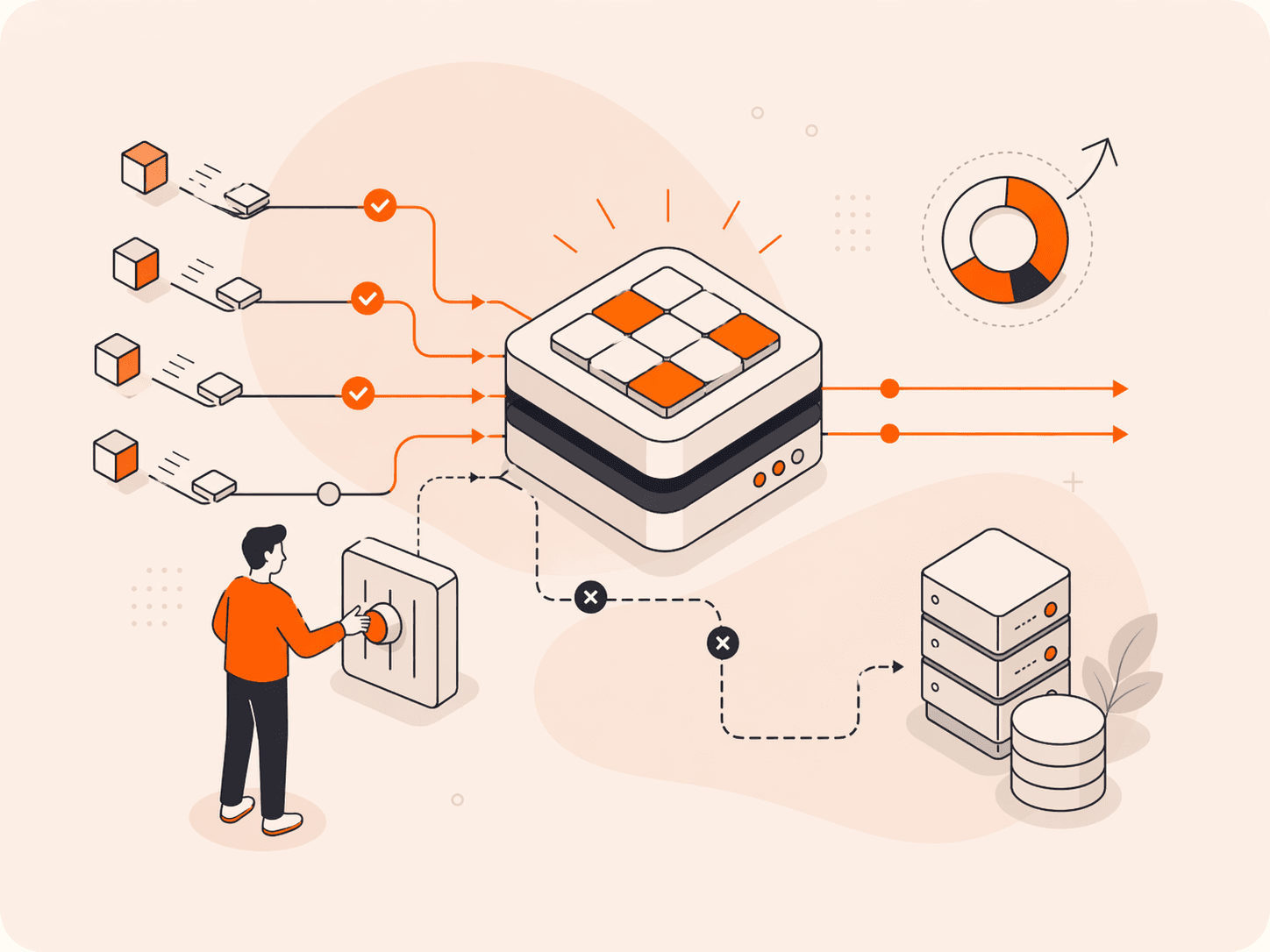
- Scalability. AIaaS enables businesses to dynamically scale their AI resources up or down based on real-time needs. This adaptability is crucial for handling varying workloads efficiently without overinvesting in unused capacity. For example, a retail company could scale up its AI resources during the holiday season to analyze consumer behavior and demand, and scale down afterwards to minimize costs.
- Flexibility. AIaaS offers the flexibility to customize the infrastructure according to specific project requirements. This means that businesses can deploy different configurations and technologies swiftly to support diverse AI applications, from machine learning model training to real-time data analysis.
| Project Type | Resource Adjustment | Benefit |
| Data Analysis | Increase compute power | Enhanced speed and accuracy of data processing |
| Machine Learning Training | Increase GPUs for training | Faster model training times |
| Real-Time Applications | Increase bandwidth and storage | Smoother operation and data handling |
| Seasonal Demand | Temporary resource boost | Cost-effective management of peak loads |
#3 Enhanced Speed and Performance
Dramatically boosting the speed and performance of AI model training and inference, this type of infrastructure becomes an essential tool for organizations aiming to enhance their AI operations.
- Accelerating Model Training. AIaaS platforms offer high-performance computing (HPC) resources like advanced GPUs and CPUs, essential for swiftly training complex AI models. For example, Gcore utilizes a cluster of Graphcore servers specifically designed for machine learning tasks. These servers boast high specifications and are optimized to process large volumes of data quickly. By using such powerful resources, organizations can significantly reduce the time required for training, which is crucial for projects that need fast iterative testing and rapid model deployment.
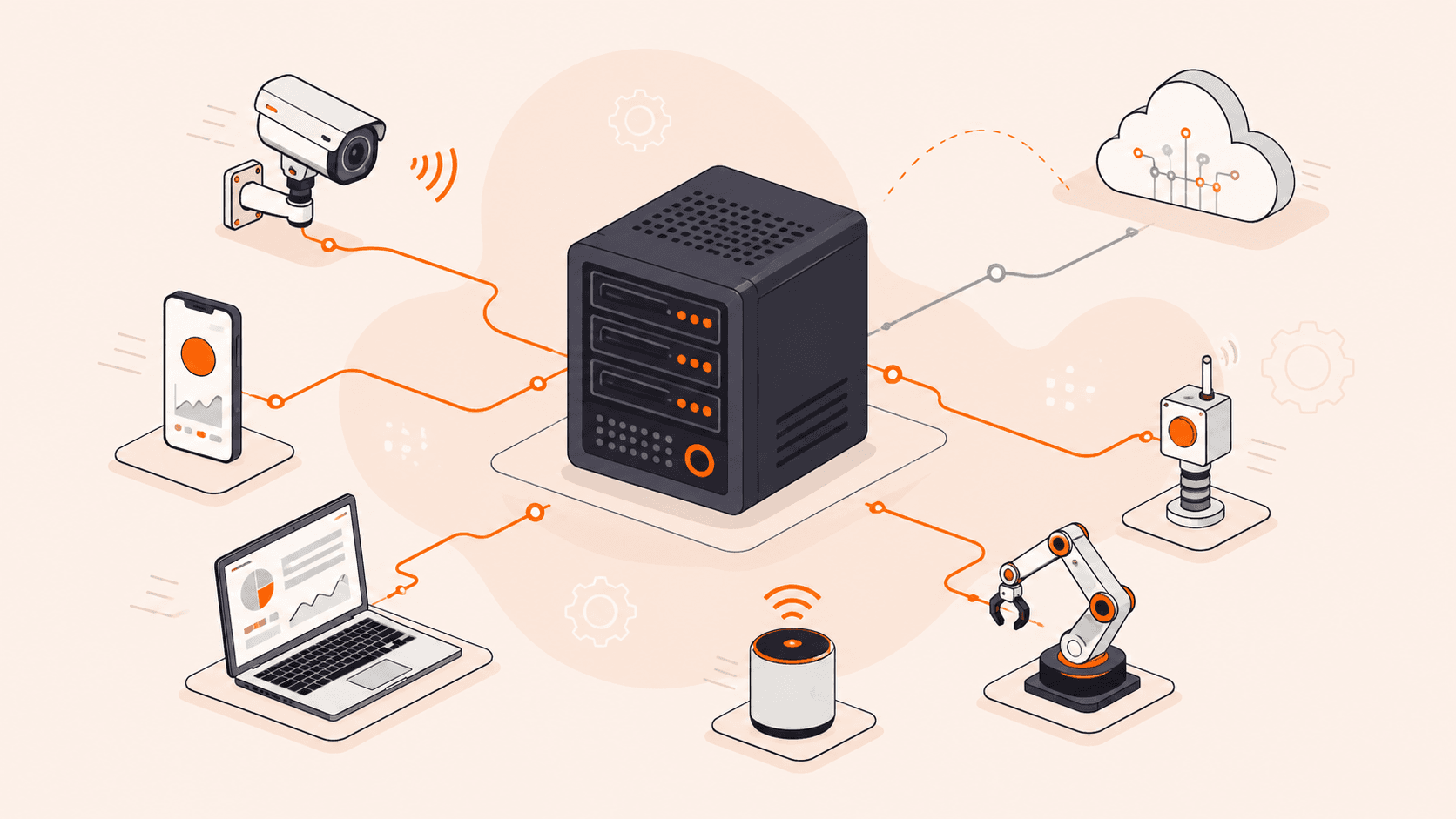
- Enhancing Inference Capabilities. Inference applications such as fraud detection, real-time personalization, and autonomous systems rely heavily on the capacity to assess fresh data and make choices in real time. AIaaS provides optimized infrastructure that can handle massive amounts of data with low latency, improving the responsiveness of AI-powered apps. This feature means that organizations may provide better, more efficient services to their clients while eliminating the lag associated with less advanced systems.
#4 Improved Security and Compliance
AI Infrastructure as a Service (AIaaS) not only speeds up and simplifies AI operations, but it also considerably improves security and compliance with worldwide data protection requirements.
- Robust Security Measures. AIaaS companies use reliable security mechanisms to safeguard sensitive data and AI models against unwanted access and cyber threats. These safeguards frequently include data encryption in transit and at rest, regular security audits, and multi-factor authentication systems. Businesses can benefit from top-tier security technologies and procedures by leveraging the expertise of AIaaS providers, which may be too hard or expensive to execute on their own.
- Compliance with Global Regulations. AIaaS systems are designed to comply with important global data protection legislation like the General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) in the United States, and other comparable standards around the world. Compliance is eased by the providers’ ongoing monitoring and updating of their systems to conform with legal requirements, minimizing the load on enterprises to keep up with these changing standards.
- Enhanced Control and Monitoring. AIaaS setups also provide increased control over data and processes, as well as sophisticated logging and monitoring options. This enables firms to reliably track data access and processing, which is required for audits and compliance inspections. The capacity to respond rapidly to suspected data breaches and automatically enforce compliance regulations adds to the trust in AIaaS systems.
#5 Management and Maintenance
AI Infrastructure as a Service (AIaaS) greatly simplifies AI system management and maintenance, providing a more streamlined approach that reduces the workload on in-house IT personnel.
- Outsourcing Infrastructure Management. Outsourcing the management of AI infrastructure to AIaaS providers has numerous significant benefits. For starters, it relieves enterprises of the technical complexity of deploying, operating, and maintaining AI hardware and software. AIaaS companies handle all aspects of infrastructure management, including upgrades, scaling, and security, ensuring that AI systems perform properly without the need for ongoing scrutiny from the client’s IT personnel.
- Reduced Need for In-House Expertise. One of the major problems in applying AI is the need for specialized knowledge. AIaaS addresses this issue by granting access to cutting-edge AI technologies controlled by specialists. This approach considerably eliminates the need for firms to recruit AI specialists, which can be an expensive and time-consuming endeavor. Instead, businesses can focus on teaching their current employees to properly use AI outputs, which is frequently a more efficient use of resources.
- Operational Efficiency and Cost Savings. Businesses can improve their operational efficiency by transferring technical management to AIaaS providers. They can shift their focus from managing complex AI operations to utilizing AI insights for strategic and essential business objectives. This change not only increases productivity but also leads to significant cost savings due to lower human costs and eliminated expenses associated with purchasing and maintaining AI infrastructure.
Choosing the Right AI Infrastructure
Choosing the proper type of AI infrastructure is determined by a number of factors, including your individual use cases, the scale of AI activities, budget limits, and desired flexibility. To learn more, see our article on the development of AI infrastructure.
Conclusion
The benefits of AI Infrastructure as a Service (AIaaS) for training and inference are evident, ranging from cost savings and increased security to simpler management and operational agility. Businesses that use AIaaS may focus on innovation and core activities while specialists handle the heavy lifting of infrastructure maintenance.
If you’re looking to take your AI projects to the next level, Gcore’s AI Infrastructure could be just what you need. Our approach, designed exclusively for AI and compute-intensive workloads, takes advantage of GPUs’ hundreds of cores to accelerate AI training and manage the high demands of deep learning models.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.