In today’s digital landscape, the cost of a data breach can be staggering, with an average price tag of $4.3 million. The demand for robust cybersecurity solutions is increasing as clients and industries require businesses to uphold a certain level of security. This means that investing in cybersecurity is not a typical expense, but a business-savvy, financially wise strategy. In this article, we’ll explore what cybersecurity solutions are, what options exist, how to choose, implement, and optimize the right strategy for your business, and trends for 2023.
What Are Cybersecurity Solutions?
Cybersecurity solutions encompass a wide range of tools, technologies, and services designed to mitigate cyber threats and protect digital assets from unauthorized access, data breaches, and other malicious activities. Cybersecurity solutions play a critical role in maintaining the confidentiality, integrity, and availability of information systems and safeguarding sensitive data, ensuring the smooth operations of your business in all industries and of all sizes. Common examples of such solutions are employee training programs, antivirus software, and firewalls.
Baseline Cybersecurity Solutions
To safeguard against cyber threats, it is not always necessary to invest in complicated and expensive solutions. Phishing and ransomware are significant risks for businesses of all sizes, in both the public and private sectors. Yet, effective remedies for these attacks can be achieved through training, data protection, and access control.
This section provides an overview of essential cybersecurity solutions suitable for any company with digital operations. These solutions are particularly valuable for businesses with limited cybersecurity budgets or those in their early stages of cybersecurity implementation.
Cybersecurity Training
One critical solution for mitigating cyber threats is cybersecurity training: educating employees or users about your company’s digital assets, vulnerabilities, and risks. The primary goal is to raise awareness of potential cyber threats and attacks and equip individuals with the ability to identify, respond to, and report incidents.
Training should be interesting, relevant, and actionable. Different teams may require specific training; a business might offer a general course on phishing attacks and a specific course for developers on secure coding.
Examples of solution providers in this domain include KnowBe4, SANS, and Proofpoint. Some of these programs offer free content, including products, tools, cheat sheets, and tutorials.
Training should not be a one-time event. Regular educational programs must be implemented to keep users and employees informed about evolving threats, hacker techniques, and new protection tools.
Data Protection
Data protection solutions aim to secure your company databases, safeguarding against critical data losses caused by hardware failures, human error, or software malfunctions resulting from cyberattacks.
One effective data protection solution is an encrypted cloud backup program, which regularly automatically copies your data to secure cloud locations. Backup encryption provides an additional layer of protection, rendering the data unreadable and unusable even if hackers gain unauthorized access to your backup. Solution providers in this space include NordLocker, Acronis, Idrive, and CrashPlan.
Access Control
Access control solutions ensure that only authorized users can access your systems. Strong passwords alone are no longer sufficient, as hackers use a range of methods such as phishing attacks, social engineering, automated password guessing, and malware to steal credentials. Access control solutions are particularly important for remote teams, where employees access systems via insecure networks, often on personal devices.
The most easily implementable and important access control solution for your business is multi-factor authentication (MFA), which prevents 30–50% of access-related cyberattacks. MFA requires users to provide multiple forms of identification. A common example of MFA is when users enter a password and a uniquely generated code is sent to their mobile device to log in.
MFA software can be purchased as a standalone app or API integrated into a company’s application. Examples of MFA solution providers include Google Authenticator, LastPass, and Okta.
Advanced Cybersecurity Solutions for Enhanced Protection
As the digital footprint of a business grows and partnerships with prominent brands are established, business assets become more valuable to hackers. At this stage, it is recommended to invest in advanced cybersecurity solutions, and to have those solutions in place before the business becomes overexposed to cyber threats. If feasible, hiring a cybersecurity professional or outsourcing cybersecurity will help to ensure effective management and implementation of current best practices.
Network Protection
Network protection solutions are essential in preventing unauthorized access to network resources and swiftly identifying and thwarting cyberattacks. As most company devices are connected to networks like Wi-Fi (WLAN,) local area network (LAN,) wide-area network (WAN,) or enterprise private network (EPN,) securing these networks is imperative as businesses scale and have a larger external attack surface.
Network cybersecurity solutions operate on two levels: preventing hackers from infiltrating the network and safeguarding individual resources within the network (including devices, software, and data) in the event that external controls are breached.
Prominent network cybersecurity solutions include:
- DDoS protection: DDoS protection solutions are defensive measures that monitor traffic to mitigate and prevent distributed denial-of-service (DDoS) attacks, safeguarding networks and online services by filtering and blocking malicious traffic.
Network cybersecurity solutions are an overarching category, and as such some of the solutions discussed in the remainder of this section also pertain to network security.
Endpoint Protection
In the landscape of remote work and device proliferation, ensuring robust endpoint protection has become paramount to safeguarding sensitive company data. From laptops and mobile phones to wearables, medical devices, scanners, and Internet-of-Things (IoT) devices, endpoints serve as potential gateways for cyber attacks, making effective security solutions indispensable.
Statistics from IBM reveal that a staggering 70% of data breaches stem from vulnerabilities in endpoint devices. With personal devices regularly utilized for work purposes and work devices occasionally used for personal activities, the risk landscape has expanded exponentially.
To combat these threats, organizations must deploy comprehensive endpoint cybersecurity solutions. Such solutions are designed to be installed directly on individual devices, systematically analyzing their files, processes, and systems to identify any signs of suspicious or malicious activity. Examples of widely used endpoint protection solutions include Crowdstrike, Sophos, Kaspersky, and SentinelOne.
Enterprise Endpoint Protection Solutions
While traditional antivirus software has long served as the primary defense mechanism, its effectiveness is limited to only a few devices. Enterprises require more robust cybersecurity solutions, such as an enterprise protection platform (EPP,) endpoint detection and response (EDR,) and extended detection and response (XDR.) Note: the least protective is EPP, and the most protective is XDR.
EPP acts as a proactive shield, preemptively preventing attacks on endpoints. However, given the sophistication of modern threats, relying solely on EPP may not suffice. EDR provides advanced threat detection and response capabilities, specifically designed to identify and neutralize threats that might have slipped past EPP defenses. Recognizing the need for comprehensive protection, cutting-edge cybersecurity solutions now integrate both EPP and EDR functionalities into a unified platform. This consolidation enables organizations to fortify their defenses, achieving a higher level of endpoint security.

Nevertheless, effective endpoint protection extends beyond individual devices. Attacks can manifest across various domains, including databases, applications, networks, and cloud workloads. To address these broader threat landscapes, organizations are turning to extended detection and response (XDR) solutions. XDR entails a holistic approach, extending protection beyond endpoints and incorporating multi-dimensional threat response capabilities.
Audit Log Management
Audit logging cybersecurity solutions document activity within an organization’s software. These activities encompass a wide range of events, including database access and modifications, administrative actions, and login failures. With the power to decide which specific activities to track, companies can gain invaluable insights from audit logs, revealing precisely when an event occurred, the corresponding timestamp, and the user responsible.
The significance of audit logging extends far beyond mere documentation. These comprehensive logs serve as a valuable resource for security teams when investigating potential breaches. By analyzing the audit trail left behind, security professionals can unravel the sequence of events that led to a security incident. This forensic capability not only aids in understanding the nature and scope of the breach but also plays a pivotal role in implementing effective remediation measures.
Audit logging cybersecurity solutions can be implemented as standalone tools or may be found within broader security frameworks, such as security information and event management (SIEM) and identity and access management (IAM) solutions. Leading cloud service providers and database management systems often incorporate robust audit logging capabilities as an integral part of their offerings.
By leveraging comprehensive audit log management, organizations can strengthen their security posture, ensuring adherence to regulatory compliance standards and enabling proactive threat detection. Furthermore, the wealth of information stored within audit logs can be utilized for fine tuning security policies, identifying potential vulnerabilities, and improving overall system performance.
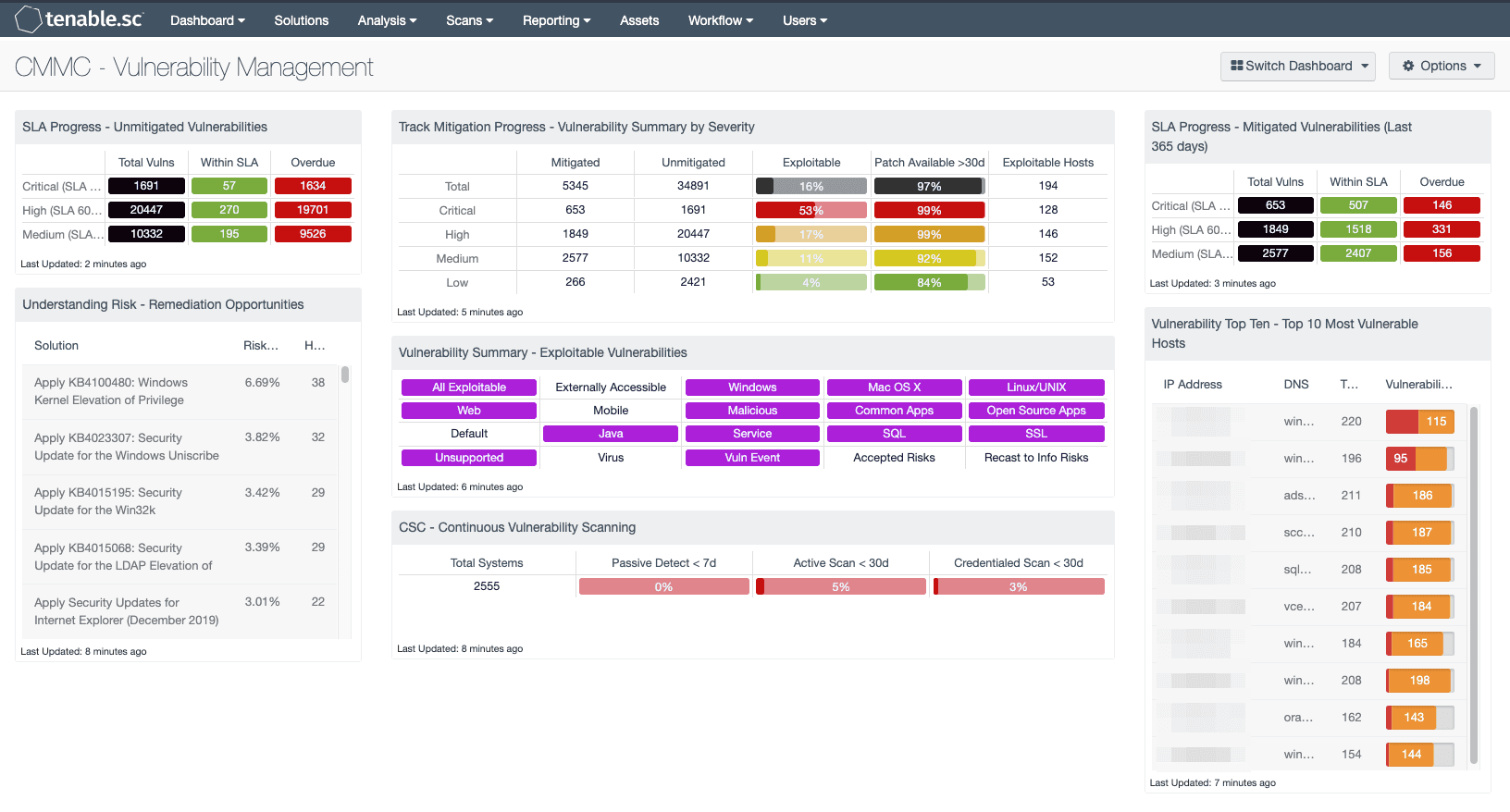
Vulnerability Management
Robust vulnerability management cybersecurity solutions play a crucial role in identifying, prioritizing, and remedying weaknesses in computer systems, networks, and software. Such vulnerabilities encompass a wide array of potential risks, including unpatched bugs, outdated systems or software, and misconfigurations of both software and hardware components.
While manual vulnerability management is hypothetically possible, it is time consuming and error prone, even for smaller organizations. To streamline and automate these critical operations, security teams rely on specialized vulnerability management software. These powerful cybersecurity solutions oversee the entire lifecycle of vulnerability management, encompassing identification, remediation, and comprehensive reporting.
Enterprise Vulnerability Management Solutions
In addition to comprehensive vulnerability management software, standalone solutions such as vulnerability scanners and patch management tools are also available. Vulnerability scanners focus on identifying and listing vulnerabilities, serving as a first step towards risk mitigation. They can function as an entry point to advanced cybersecurity for organizations with limited budgets, providing an initial assessment of vulnerabilities. However, interpreting and prioritizing the identified vulnerabilities typically requires the expertise of a dedicated security specialist who can guide the remediation efforts effectively.
Patch management solutions take a more proactive approach than vulnerability scanners by identifying, acquiring, testing, and installing necessary software patches on devices, ensuring that critical vulnerabilities are quickly addressed. Patch management cybersecurity solutions are predominantly utilized by IT teams, particularly in larger organizations with extensive software ecosystems to oversee. These solutions streamline the process of managing patches across a myriad of devices, ensuring that critical updates are promptly implemented to mitigate potential risks.
Notable examples of vulnerability management solutions include Tenable Nessus and Rapid7 InsightVM, both renowned for their robust feature sets and proven track records in the industry.
Penetration Testing
Penetration testing (or “pen testing”) is a crucial cybersecurity service that evaluates the security posture of systems by simulating cyberattacks. It offers a comprehensive approach for identifying vulnerabilities, surpassing the scope of traditional vulnerability assessments.
Before conducting a penetration test, a clear scope is defined, outlining the specific areas to be assessed. This can include software, hardware, networks, and even the human element through simulated attacks on employees. By subjecting systems to controlled cyberattacks, organizations gain valuable insights into their security defenses and can proactively address vulnerabilities before they are exploited by malicious actors. Penetration testing plays a pivotal role in uncovering weaknesses that may be overlooked by traditional security assessments, thereby enhancing overall resilience and minimizing potential risks.
Penetration testing services are offered by independent security professionals, specialized penetration testing companies, and managed security service providers (MSSPs). Prominent solution providers in the field of penetration testing include Bugcrowd, HackerOne, ImmuniWeb, and Gcore.
Specialized Solutions
When it comes to protecting specific technologies, specialized solutions are essential. There are three main types of specialized solutions, aimed respectively at applications, cloud, and IoT. Let’s look at each in turn.
Application Security
Application security solutions play a critical role in safeguarding the software that drives business operations. From design to production, these solutions provide an additional layer of protection, mitigating the impact of potential attacks.
There are various types of application security solutions available, each addressing specific aspects of application protection:
- Web application firewalls (WAFs): WAFs act as gatekeepers, protecting all your web resources, including web applications and APIs, against unauthorized access to confidential data. By monitoring traffic in real time, WAFs can enforce preset rules to block malicious requests and thwart potential attacks. Gcore WAF is an example of such a solution. Our tool utilizes machine learning to monitor application traffic and promptly block access if malware is detected.
- Static application security testing (SAST): SAST focuses on reviewing an application’s code to identify common coding errors, insecure coding practices, and known security weaknesses. By analyzing the codebase, SAST tools help developers proactively address vulnerabilities during the development lifecycle.
- Dynamic application security testing (DAST): DAST takes a different approach by monitoring a running application and performing real-time penetration testing. By sending various unusual or malicious inputs to the application, DAST tools evaluate how it responds and detects potential vulnerabilities or bugs. Developers receive detailed reports highlighting identified vulnerabilities.
Veracode and Checkmarx offer both SAST and DAST functionality.

- Runtime application self-protection (RASP): RASP solutions take application security a step further, residing inside the application environment itself. Embedded in the runtime environment, RASP can accurately distinguish between malicious and legitimate actions. Fortify is one well-known example of RASP.
Cloud Security
Cloud security solutions safeguard assets hosted in cloud environments. These solutions encompass both on-premises network security measures, such as firewalls, VPNs, and intrusion detection systems, as well as cloud-specific solutions.
Cloud workload protection platforms (CWPPs) monitor the usage of cloud resources by specific applications and detect any suspicious activities. Acting as intermediaries, cloud access security brokers (CASBs) provide an additional security layer between cloud users and providers. Cloud security posture management solutions (CSPM) focus on identifying and resolving cloud misconfigurations.
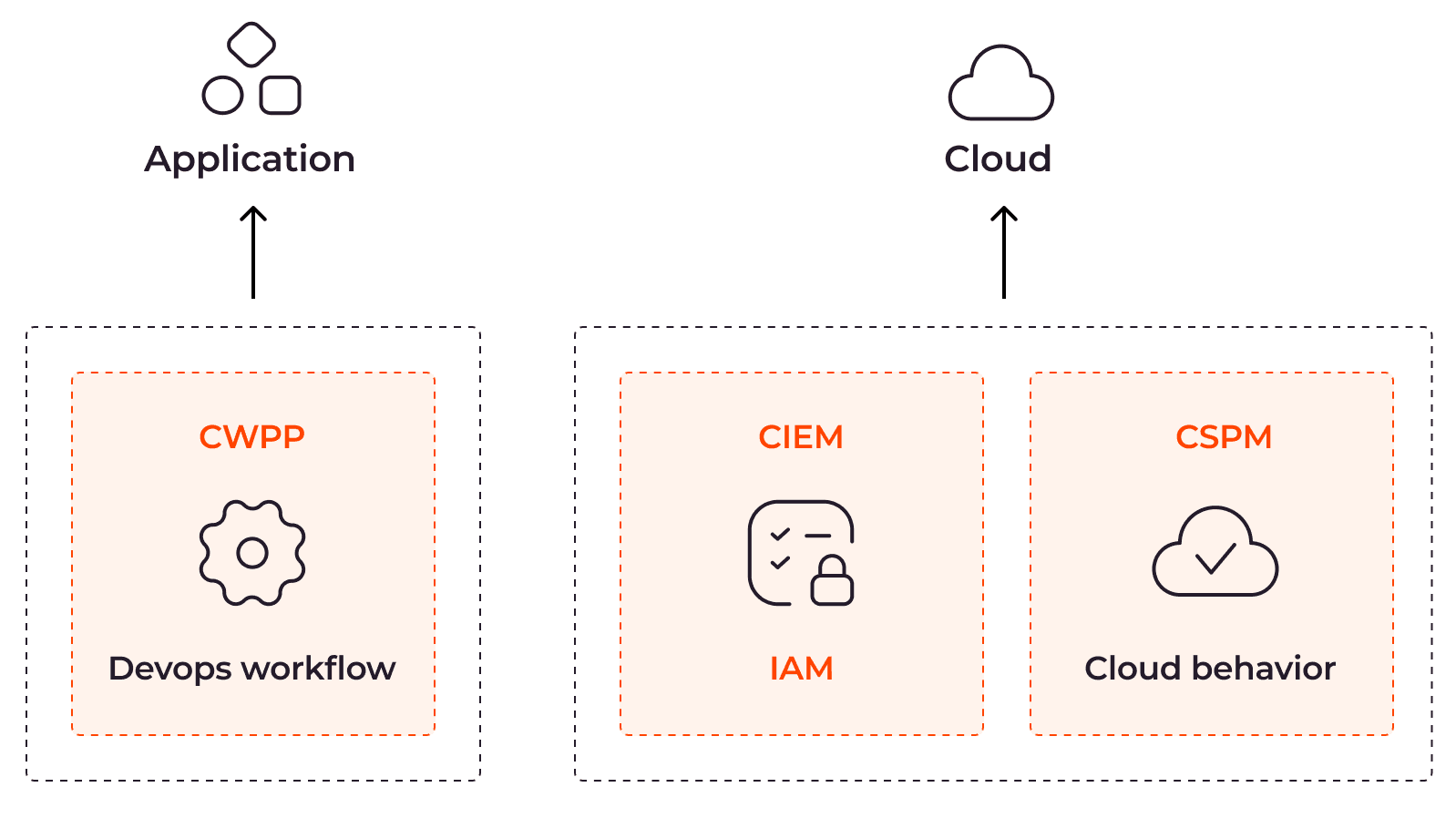
While many cloud providers offer built-in security solutions or as extensions, some organizations require specific cybersecurity controls. Third-party cloud security solutions like Sophos Central, Check Point CloudGuard, and Proofpoint deliver comprehensive protection and ensure the integrity of cloud assets.
IoT Security
IoT security solutions safeguard the wide range of devices that connect to the internet and interact with one another. This includes a wide range of technologies, such as contactless payment systems, medical smart wearables, and smart sensors.
As the IoT landscape expands, so does the potential risk. According to a 2022 report by IBM, the average cost of a data breach increases by $152,465 in an IoT environment, highlighting the urgent need for robust security measures.
IoT security is closely related to endpoint security, and many of their respective security measures overlap. Nevertheless, there are specialized security solutions designed to manage, monitor, and defend IoT devices. Prominent examples of IoT security solutions include AWS IoT Device Defender, Forescout, and McAfee Embedded Control. These solutions offer comprehensive features to detect and mitigate threats specific to IoT devices, ensuring the integrity and privacy of data transmitted between interconnected devices.
How To Optimize Your Cybersecurity Solutions: A Practical Guide
To see the return on investment (ROI) of cybersecurity solutions, it is essential to understand how to select the tools that best align with your organization’s specific cybersecurity needs, budget, and operational capacity. Merely buying numerous tools does not guarantee optimal security, so it is important to build your cybersecurity setup with intention.
#1 Create an Asset Inventory
Compile a comprehensive list of all potential entry points that cybercriminals could exploit (including internal and external attack surfaces.) This inventory will help you identify which assets require protection and guide your selection process.
#2 Review Legal and Industry Requirements
Familiarize yourself with the legal and industry-specific cybersecurity regulations relevant to your business. Ensure that your cybersecurity measures align with these requirements. Make sure to consider individual roles and responsibilities within your organization. You may need to adjust your personnel or consider outsourcing to a cybersecurity professional.
#3 Conduct a Risk Assessment
Identify vulnerabilities and assess their potential impact and likelihood of occurrence. Prioritize them based on their significance to and potential impact on your organization’s security. Deloitte’s research reports that 56% of high performing companies conduct qualitative risk assessments to optimize ROI. Use relevant questions like the ones listed below:
- Which assets are connected to your network?
- What levels of protection do the assets need?
- Who can access the assets?
- Where are the assets stored?
- How are the assets currently protected?
- What threats do the assets face?
- What internal processes (incident response plan) are in place when an incident occurs?
#4 Align with Business Goals
Your cybersecurity choices should align with your broader business objectives, growth plans, and strategic partnerships. Ensure that the solutions you select contribute to the overall success of your organization. Put in place cybersecurity infrastructure that takes into account forecasted growth.
#5 Regularly Update Cybersecurity Infrastructure
Recognize that your company’s processes are dynamic, and that changes in operations may require adjustments to your cybersecurity measures. Conduct annual reviews of your cybersecurity infrastructure, as 66% of companies with high cyber performance do.
Implementing Cybersecurity Solutions to Meet Compliance Requirements
In certain cases, implementing specific cybersecurity measures becomes necessary not only because you recognize their importance, but also due to legal requirements, insurance policies, or industry standards.
To ensure compliance and protect your business:
- Understand applicable standards: Research and explore the cybersecurity standards followed by companies in your industry or niche. This will give you insights into the best practices and requirements relevant to your business.
- Evaluate data: Assess the type and extent of data you handle. Understanding the sensitivity and criticality of the data will help you determine the level of security measures required to protect it adequately.
- Weigh compliance benefits: Compare the benefits of compliance with potential consequences of non-compliance. While some requirements may be recommended but not obligatory, it is essential to consider the potential risks and liabilities associated with non-compliance.
Here are some examples of common regulations that require specific cybersecurity solutions:
- Health Insurance Portability and Accountability Act (HIPAA): If you handle personal health information, compliance with HIPAA is mandatory. This regulation necessitates the implementation of access control, audit logging, and data protection solutions to safeguard sensitive healthcare data.
Outsourcing Cybersecurity
In today’s dynamic threat landscape, many businesses, regardless of their size, choose to outsource part or all of their cybersecurity management to specialized third-party providers. This strategic decision offers numerous advantages, including cost-effectiveness, access to expertise, round-the-clock coverage, and cutting-edge technologies.
According to IBM, organizations that opt for managed security services can reduce the average cost of data breaches by $69,100, emphasizing the value of outsourcing. There are several common options for outsourcing cybersecurity:
- Specialized managed security solutions: These services provide you with a tool and help you to manage it. For example, Gcore offers managed network and application cybersecurity solutions, including advanced DDoS protection services.
By outsourcing cybersecurity to external providers, businesses can tap into a wealth of knowledge and experience, ensuring robust protection against evolving threats while reducing the burden on in-house employees. The expertise, resources, and advanced technologies offered by these providers enable organizations to strengthen their security posture, while also benefiting from cost savings and round-the-clock vigilance.
Top Cybersecurity Solutions Trends In 2023
The evolving cybersecurity landscape is driving significant changes and innovations in cybersecurity solutions, particularly impacting enterprises and industries with high cybersecurity dependencies, like finance, healthcare, and retail. However, it is crucial for all organizations in all sectors and of all sizes to stay informed about these trends in order to optimize their cybersecurity efforts and return on their cybersecurity investment. Let’s explore three of the top cybersecurity trends for 2023: AI, zero trust, and quantum-safe cryptography.
Artificial Intelligence
The widespread adoption of AI extends to cybersecurity. Cybersecurity providers are actively integrating machine learning capabilities into their solutions. In fact, by 2025, around 82% of IT and security decision-makers plan to invest in AI-driven cybersecurity solutions.
AI enhances various aspects of cybersecurity, particularly the detection of, and response to, malicious activities. AI algorithms can identify unknown vulnerabilities by analyzing patterns derived from previous attacks. The automation and speed offered by AI significantly improve detection capabilities, reduce costs, and deliver more precise results. AI can even uncover hidden patterns that may go unnoticed by human analysts.
Zero Trust Framework
The concept of zero trust challenges the traditional notion of trust within networks, emphasizing the need for continuous verification of all network requests, assuming breach, and adopting the principle of least privilege access. This approach addresses the evolving business landscape, including the need to secure remote workers, manage hybrid cloud environments, and combat ransomware attacks.
Zero-trust technologies encompass a range of security measures, including risk-based multi-factor authentication, continuous threat monitoring, network microsegmentation, and reliable cloud workload verification. These technologies aim to ensure the authentication and authorization of users or systems while maintaining a high level of security.
Gartner forecasts that by 2026, 10% of large companies will have mature zero-trust programs in place, a significant increase from less than 1% in 2023. Recognized organizations have already established standards, such as NIST 800-207, which can guide companies in implementing a zero-trust infrastructure.
A growing number of cybersecurity solutions are built upon the principles of zero trust. Examples include multi-factor authentication (MFA,) zero trust network access, and secure access service edge (SASE) solutions.
Businesses that stand to benefit the most from implementing zero-trust solutions include those looking to protect their cloud environments and/or manage legacy systems, SaaS applications, and unmanaged devices, as well as those subject to industry or compliance requirements. By adopting a zero-trust approach, organizations can strengthen their security posture, mitigate risk, and safeguard their critical assets in an increasingly complex and interconnected digital landscape.
Quantum-Safe Cryptography
As quantum computing continues to advance, it poses a significant threat to traditional encryption methods. Once quantum computers become widely accessible, the ability to break encryption that would have taken classical computers millions of years will be achievable within hours or even minutes by cybercriminals. To address this imminent challenge, the concept of quantum-safe cryptography emerges as a viable solution.
Although quantum computers are not available today, the pace of technological progress is rapid. For instance, in May 2023 IBM opened access to its latest Osprey Quantum Processor, boasting an impressive 413 Qubits. Such advancements indicate that the era of practical quantum computing is drawing closer.
Recognizing the need for quantum-resistant encryption, the US Department of Commerce’s National Institute of Standards and Technology (NIST) has taken a proactive role. NIST announced the development of a post-quantum cryptographic standard, which is expected to be finalized by 2024. This standard will provide guidelines for implementing cryptographic algorithms that can withstand attacks from powerful quantum computers.
Considering these developments, it is crucial for any organization that relies on encryption to prepare for the quantum computing era. This involves understanding the potential impact on their current security infrastructure and implementing quantum-safe cryptographic solutions. Organizations can either undertake this transition independently or choose to partner with a trusted managed security service provider (MSSP) that specializes in quantum-safe cryptography. An experienced MSSP can guide organizations through the process, ensuring a smooth transition and maintaining the highest level of data security.
Conclusion
The rise of cyber threats and hacking tool availability makes it essential for businesses to prioritize cybersecurity measures. Unprepared organizations are prime targets, necessitating baseline cybersecurity tools to protect critical digital assets. However, a strategic approach to cybersecurity investments is crucial, as adopting expensive or trendy solutions doesn’t guarantee protection. To ensure ROI and effective cybersecurity, businesses should conduct risk assessments, consider compliance requirements, and align security measures with business plans and objectives. By making informed decisions and implementing the right cybersecurity toolkit, businesses can boost resilience against evolving threats, safeguard digital assets, and operate securely in the digital age.
To assist you in navigating the complex landscape of cybersecurity solutions, we invite you to explore Gcore’s security tools—like DDoS Protection—or consult our experts. Our resources provide valuable insights and guidance on selecting the most suitable cybersecurity solutions for your organization.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.