Keyloggers are hardware or software that record keyboard input by capturing all keystrokes typed on a keyboard, including usernames and passwords. Keyloggers can be used for helpful, legal reasons, or cause harm when used by malicious actors. In this article, we explain what keyloggers are and how they work, how to detect keylogger activity, and how to remove keyloggers. You’ll also learn personal and enterprise-level protective measures against malicious keyloggers.
What Are Keyloggers?
Keyloggers, also known as keystroke loggers or keyboard capturers, are specialized hardware or software that capture keyboard input in real time. They capture all keystrokes typed on a keyboard. This includes sensitive information such as usernames and passwords. Keyloggers can even record keystrokes from hardware and on-screen keyboards including numerical keys and special characters.
Individuals, businesses, and governments utilize keyloggers for various purposes, both legitimate and malicious. Parents employ keyloggers to monitor their children’s online activities, safeguarding them from potential dangers and tracking interactions on platforms like WhatsApp, call logs, and even their location. Businesses use keyloggers to enhance productivity by monitoring employee behavior, especially in remote work contexts, ensuring adherence to policies like cybersecurity and data leak prevention. Government agencies may deploy keyloggers for intelligence and cybersecurity, with law enforcement using them for surveillance and fraud prevention—although unauthorized keylogging without consent or a valid warrant is often considered unethical and possibly illegal.
How Keyloggers Work
Captured keystrokes are typically stored in a specific file or location called a keylog, and then transmitted as a logfile. This logfile provides a detailed record of the online and offline activities performed on the affected device, organized and formatted in a way that enables analysis or further action by whoever is overseeing the keylogging.
The information collected by keyloggers can include websites visited, as well as sensitive data like usernames, passwords, PINs, and credit card details that were entered on those websites. Keyloggers can also be configured to capture mouse clicks, microphone inputs, webcam or screen captures, network and Wi-Fi information, system details, clipboard contents, browser history, search engine queries, and instant messaging conversations.
Types of Keyloggers: Hardware and Software
There are two primary types of keyloggers: hardware keyloggers and software keyloggers. Hardware Keyloggers are physical devices used to record keystrokes. They come in various forms, shapes, and sizes, and are connected between the keyboard and the computer’s CPU. Some hardware keyloggers can even be built into keyboards or hardware circuitry. Physical access to the target device is usually required to install and retrieve hardware keyloggers. Wireless keyloggers are an exception to this rule, as they can transmit the captured log files wirelessly to a remote location.
Software keyloggers are software programs designed to record and monitor keyboard inputs. They can be installed by the user intentionally, added by third parties (including attackers,) or unknowingly installed as a result of downloading malware or spyware from malicious websites. Software keyloggers are generally easier to install compared to hardware keyloggers, and can be more challenging to detect or remove. Some software keyloggers, known as kernel-based keyloggers, operate at the core level of the operating system, making them particularly challenging to identify and eliminate as they can hide in root folders.
| Criteria | Hardware keyloggers | Software keyloggers |
| Installation | Physically installed either between a computer’s keyboard and the PS/2 or USB port, or within keyboard circuitry | Installed by user or third party physically, or in some malicious cases installed remotely via email attachments, downloads, or compromised websites |
| Execution | Plug and play, no executable software required, independent of the operating system, and non-detectable | Runs in the background without user knowledge, may disguise itself as a legitimate process or implement rootkit functionality to evade detection |
| Logging | Captures keystrokes in real time by intercepting electrical signals sent from the keyboard to the computer | Captures keystrokes in real time by intercepting electrical signals sent from the keyboard to the computer |
| Storage | Captured keystrokes are stored within the keylogger’s built-in memory or removable SD card; some storage devices can store millions of keystrokes | Captured keystrokes may be encrypted and temporarily stored as keylogs/logfiles on the infected computer’s storage or in a hidden location before transmission |
| Timestamping | Software keyloggers may incorporate timestamping functionality on keylogs | Software keyloggers may incorporate timestamping functionality on keylogs |
| Encryption | Rarely used, but a password is required to access logfiles after retrieval of keylogger; wireless hardware keylogger memory may be protected by hardware encryption | Logs may be compressed and encrypted to improve transmission privacy, efficiency, and frequency |
| Retrieval | Often requires physical access to the victim’s device to retrieve the keylogger, except for wireless hardware keyloggers | Physical access to affected computer is not required for retrieval of keylogger and keylogs or logfiles |
| Transmission/Exfiltration | Wireless hardware keyloggers act as Wi-Fi hotspots and can live-transmit keystroke data wirelessly or via email | Keystroke data is transmitted via email or uploaded to remote FTP server |
| Analysis | Operator/attacker analyzes keylogs/logfiles for specific data | Operator/attacker analyzes keylogs/logfiles for specific data |
How Are Keyloggers Used?
Keyloggers are used by their operators to look for specific information in the data collected. Operators sift through the data looking for information that serves their specific purpose, whether benign or malicious.
Keylogger Use by Malicious Attackers
For a malicious attacker, the primary objective is to harvest sensitive information from the captured keylogs. This may include usernames, passwords, credit card details, and PINs. Armed with this information, attackers can carry out identity theft, make unauthorized financial transactions, or gain unauthorized access to various accounts and systems. They might target online banking accounts, email accounts, or social media profiles—any platform that requires login credentials. The use of keyloggers for malicious purposes is illegal and unethical.
Keylogger Use by Benign Operators
In a legitimate context, keylog data may be used by employers to ensure employee compliance with company policies, analyzing the sites visited, time spent on websites, browser history, and application usage. This information helps employers gauge productivity, adherence to cybersecurity policies, and adherence to work-related tasks. It is most commonly used for remote workers, when there is no physical oversight of the employee. Keylogger use in a legitimate context should be transparent, legal, and respect the privacy and rights of individuals being monitored.
How to Detect Keyloggers
Learning how to detect keyloggers is a crucial step in preventing potential damage from keylogging attacks. If legitimate keylogging is in place, you should have been informed about it and it should not cause the red flags mentioned in this section. These detection procedures are intended for malicious keyloggers.
Hardware keyloggers are easiest to detect by simple physical inspection of keyboard circuitry or USB and PS/2 ports. Pay particular attention to hardware additions on the computer, such as unknown memory sticks/dongles.
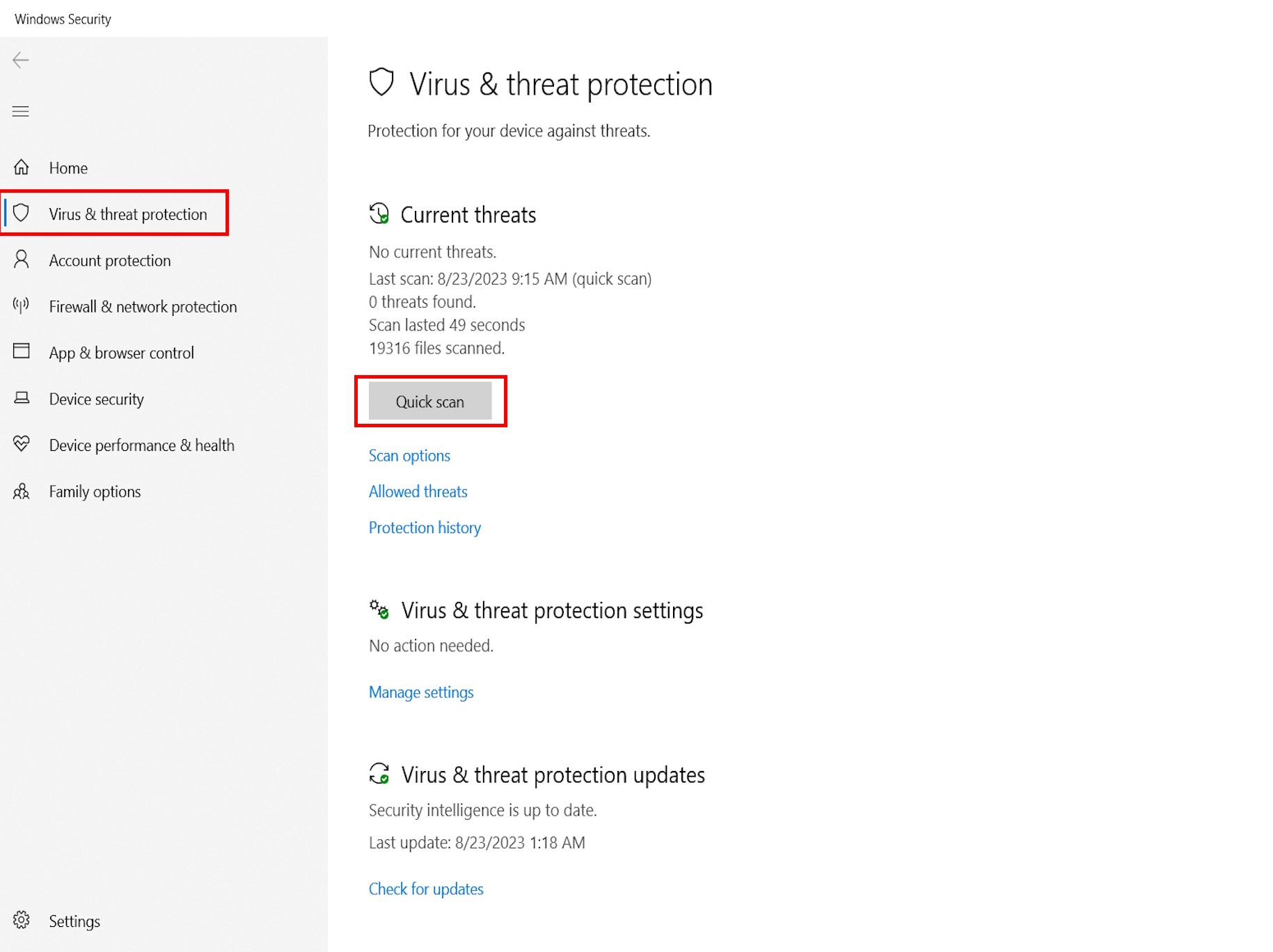
Some software keyloggers, especially those with rootkit functionality, can be challenging to detect. A powerful antivirus scan can discover keyloggers or other malware. You can also use command line (CMD) prompts or perform a quick scan on Windows to check for software loggers. Go to Windows key > Settings > Update and Security > Windows Security > Virus and threat protection > Quick scan.
In addition, the following computer behaviors can help to alert you to possible software keylogger activity regardless of your operating system.
1. Unknown programs: If you don’t recognize or remember installing a program/software/app that is on your device, it could be a keylogger installed without your knowledge.
2. Slow performance: Keylogger activity in the background may result in abnormally slow performance. Check background processes on Windows Task Manager (Windows) or Activity Monitor (macOS.)
3. Constant crashes: You may experience frequent freezes and programs crashing unexpectedly if keylogger software is in use.
4. Unusual keyboard behavior: Watch out for unusual keyboard behaviors such as automatic typing or mistyping. Though this can be caused by incorrect keyboard layout, Num Lock, outdated drivers, or a faulty keyboard—but such actions can also be caused by keyloggers.
5. Pop-ups and site redirects: Annoying pop-ups and site redirects can be indicative of either keylogging attacks or adware activity.
6. Changed browser settings: A browser-based keylogger from malicious sites can change your browser settings. These attacks use CSS scripts, Man-In-The-Browser (MITB) attacks, or web-form-based keyloggers.
7. Strange log-in notifications: Strange log-in notifications may be the result of a hacker who has obtained your login credentials via keylogging and is attempting to access your account.
8. Unsolicited authentication prompts: Unexpected or unsolicited one-time passwords (OTPs) and two-factor authentication (2FA) prompts can indicate that a threat actor has accessed your credentials using a keylogger.
9. Unknown online activity: If you log in to an online service and notice unknown activity or changed settings, someone may have accessed your account using data gathered by a keylogger.
10. Unusual network traffic: In some cases, unusual network activity may also be indicative of keylogger presence. This can usually be spotted via network traffic monitoring.
Combining several of these keylogger detection techniques maximizes the likelihood of detecting malicious keylogger activity. The next step is to put a stop to keylogging by removing the keylogger.
How to Remove Keyloggers
Once keyloggers have been detected, it is recommended to immediately take the following countermeasures to protect your business and prevent future keylogging attacks.
Physical Intervention
Remove any unknown devices from the computer, such as a USB dongle or memory stick, especially those near the keyboard. If you suspect keylogging hardware, it’s best to have a technician disassemble the keyboard and check for embedded hardware keyloggers, especially if no external devices are visible and other responses, outlined below, have been exhausted. This gives you the best chance of uncovering any malicious devices without damaging your computer.
Uninstall Unknown Programs
Remove programs, software, or apps that you don’t recognize or don’t remember installing. You may first want to use a search engine to check if those programs, software, or apps are legitimate software that you downloaded but are not in use.
To uninstall an app on Windows, press Windows key > Settings > Apps > select app > Uninstall.
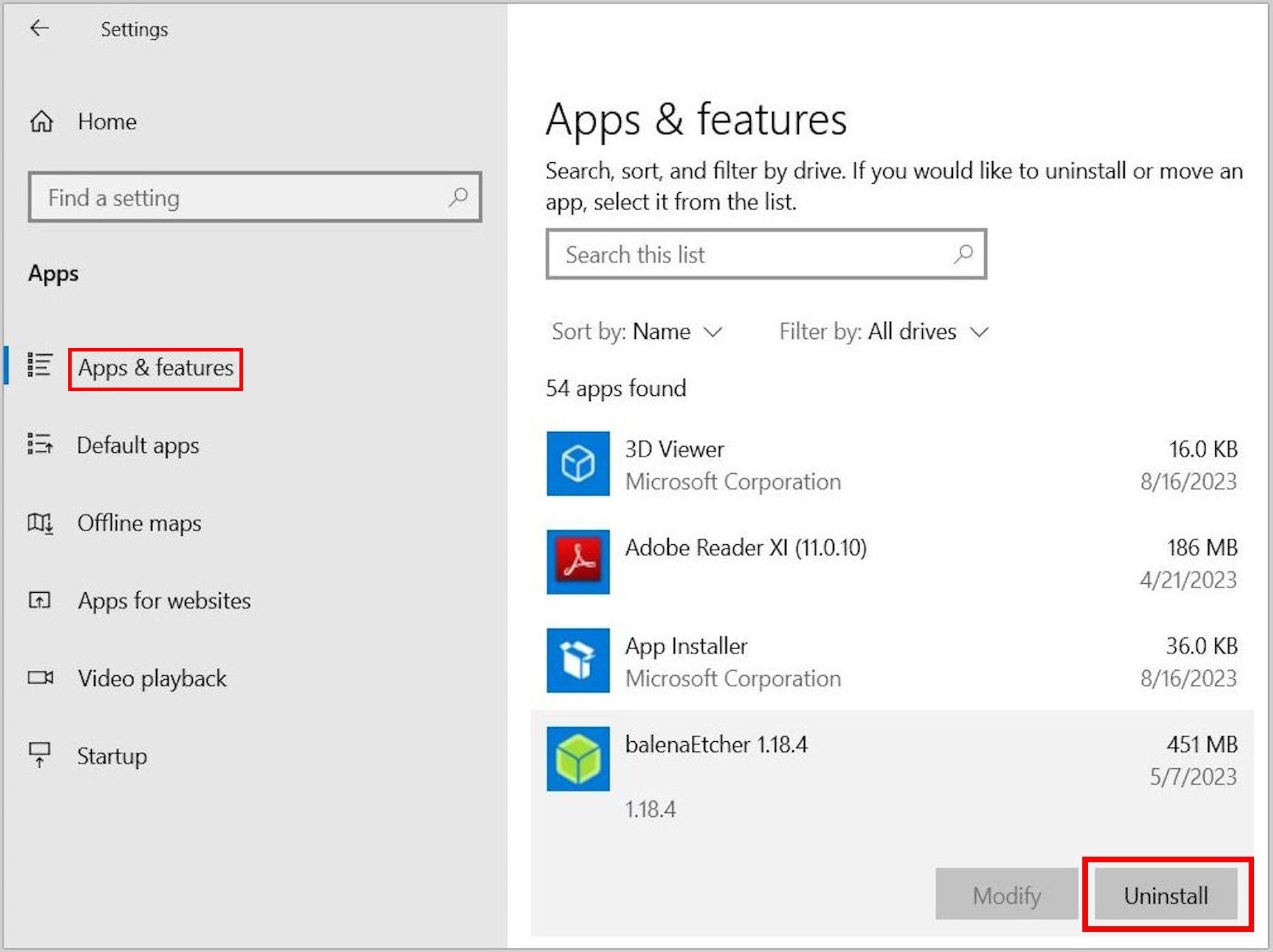
To uninstall a program on Windows via the control panel, go to Control Panel > Programs > Uninstall a program > right-click program > Uninstall.
Use Task Manager
If a known keylogger app or program doesn’t reflect on your apps or programs list, it could mean that the app is hidden. Keyloggers with rootkit functionality operate this way. In such instances, the Task Manager can be helpful in locating and removing the keylogger.
To find and remove a keylogger using the Windows Task Manager app, right-click on the taskbar to go to Task Manager or press Ctrl + Shift + Esc. Then, locate the keylogger by name, logo, or icon and right-click. This can be difficult as most keyloggers will disguise their real names. Double check app legitimacy via a search engine or ask IT personnel for clarification.
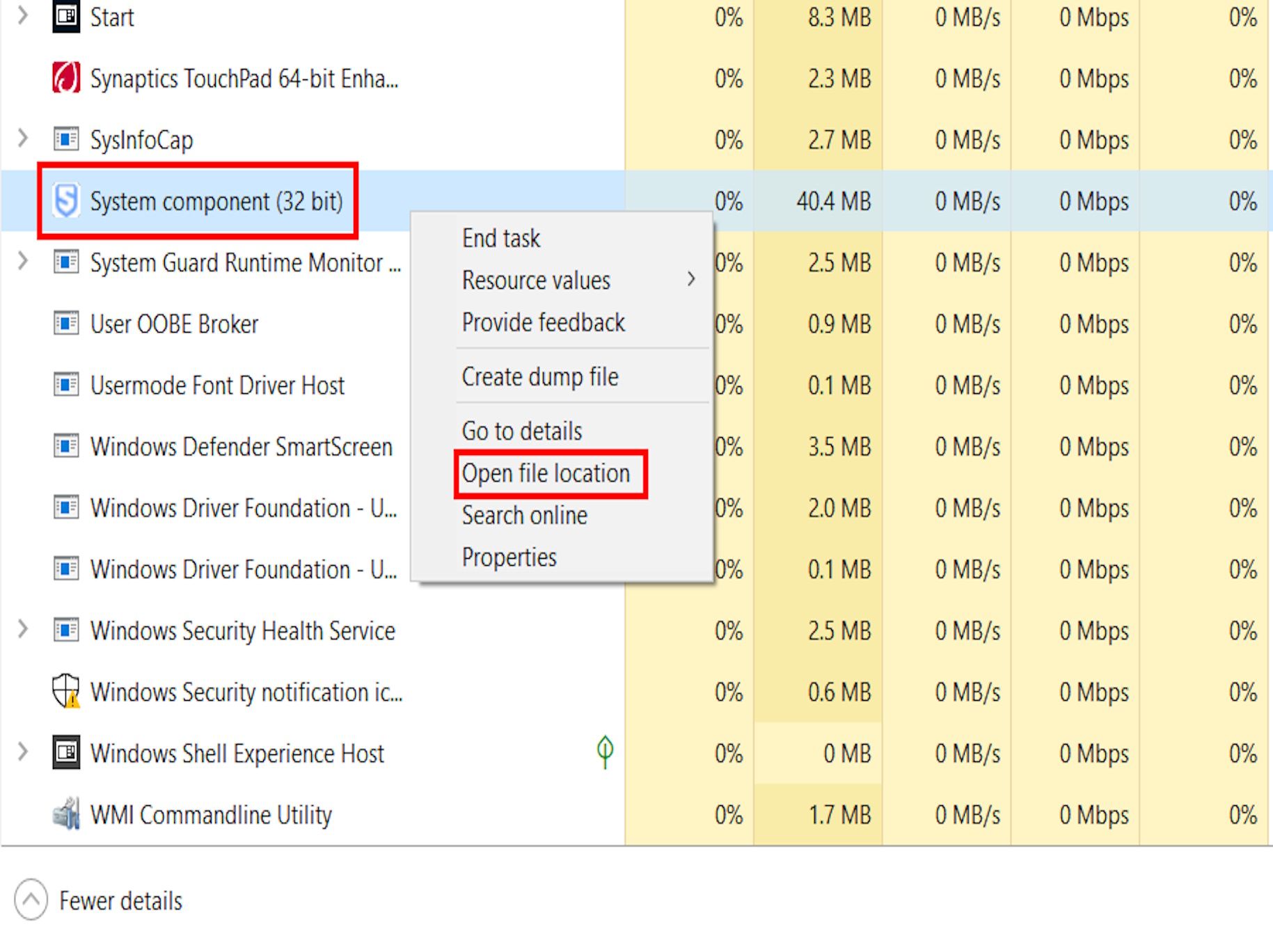
From the menu options, click Open file location. Locate and double-click the application file marked Setup/Uninstall. You can locate the particular application file by hovering your mouse pointer over all files labeled Application. When dealing with unknown files in the Windows Program folder exercise caution and double check with a simple online search.
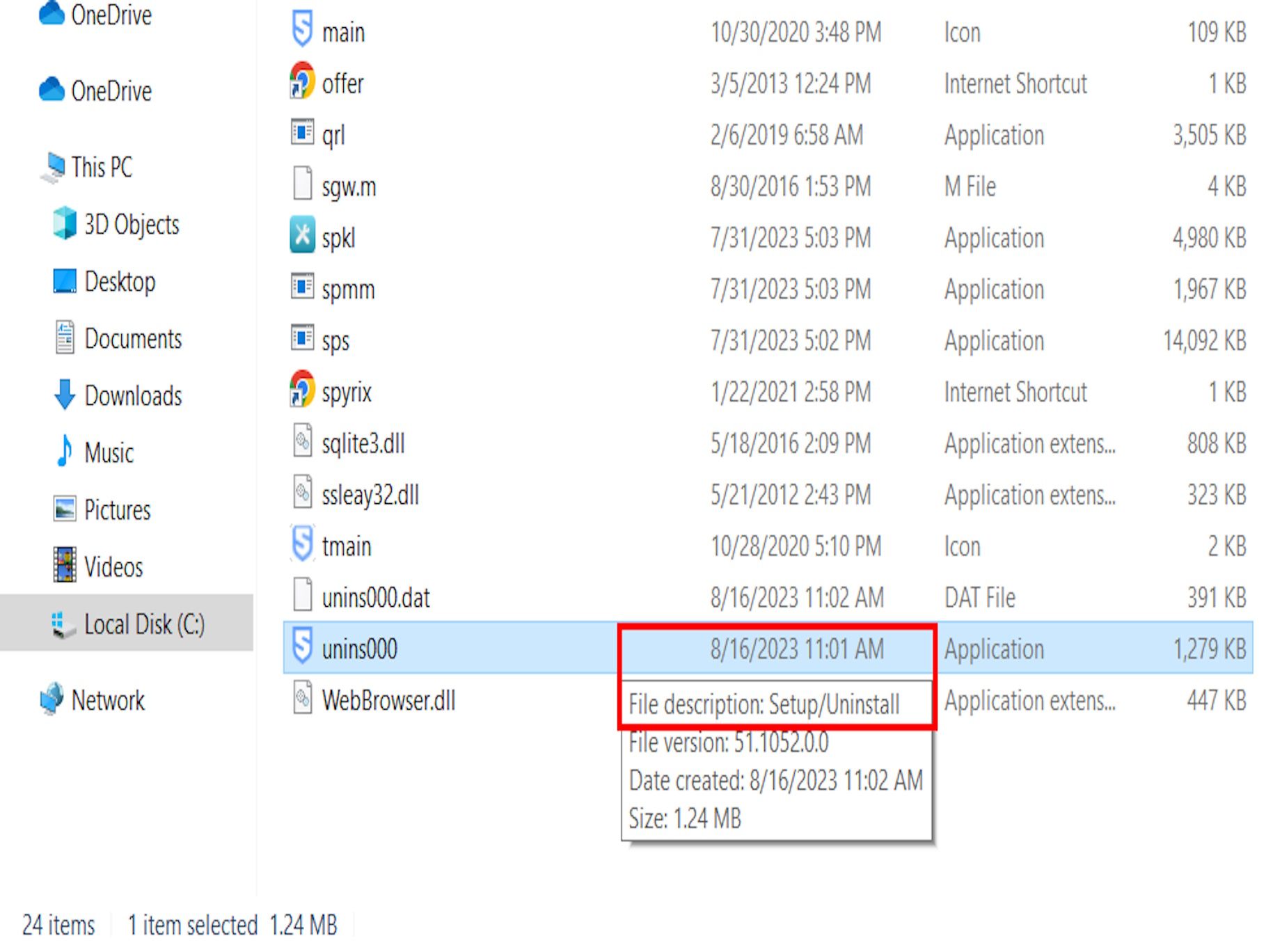
Click Yes to grant administrative permission to make changes, then click Yes to uninstall. This will completely remove the keylogger from your computer.
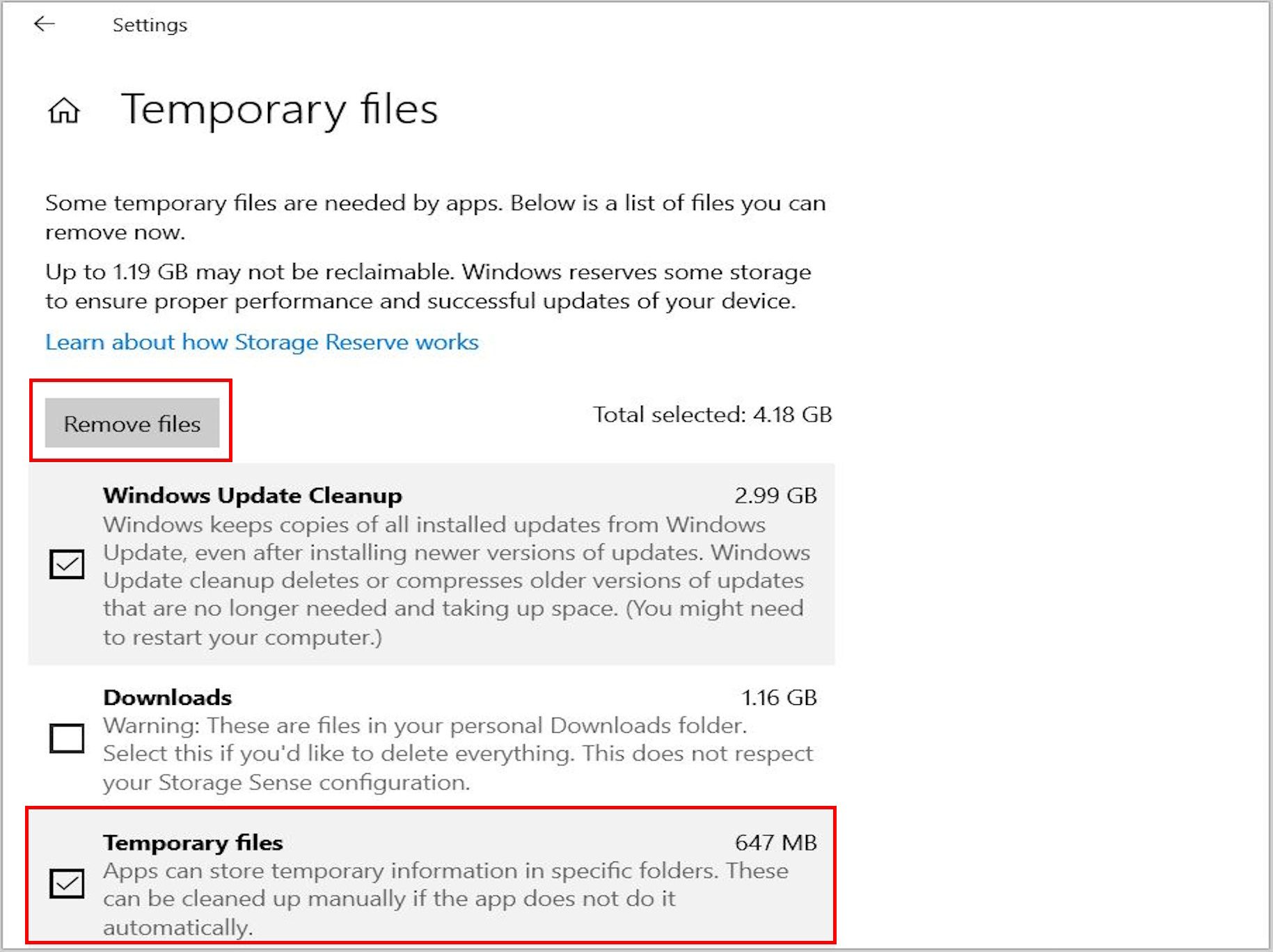
Clear Temporary Files
Keyloggers can hide in your temporary files folder. Temporary files are created to temporarily store information and free memory for other tasks. They’re also safety nets that prevent data loss when programs run. It is also important to clear temporary files on mobile devices.
To clear temporary files on Windows, press Windows key > Settings > System > Storage > Temporary files > select files > Remove files.
Restore Default Browser Settings
Browser-based keyloggers can be removed by restoring default browser settings. It is also important to restore the browser’s default settings on mobile devices if keylogger activity is suspected.
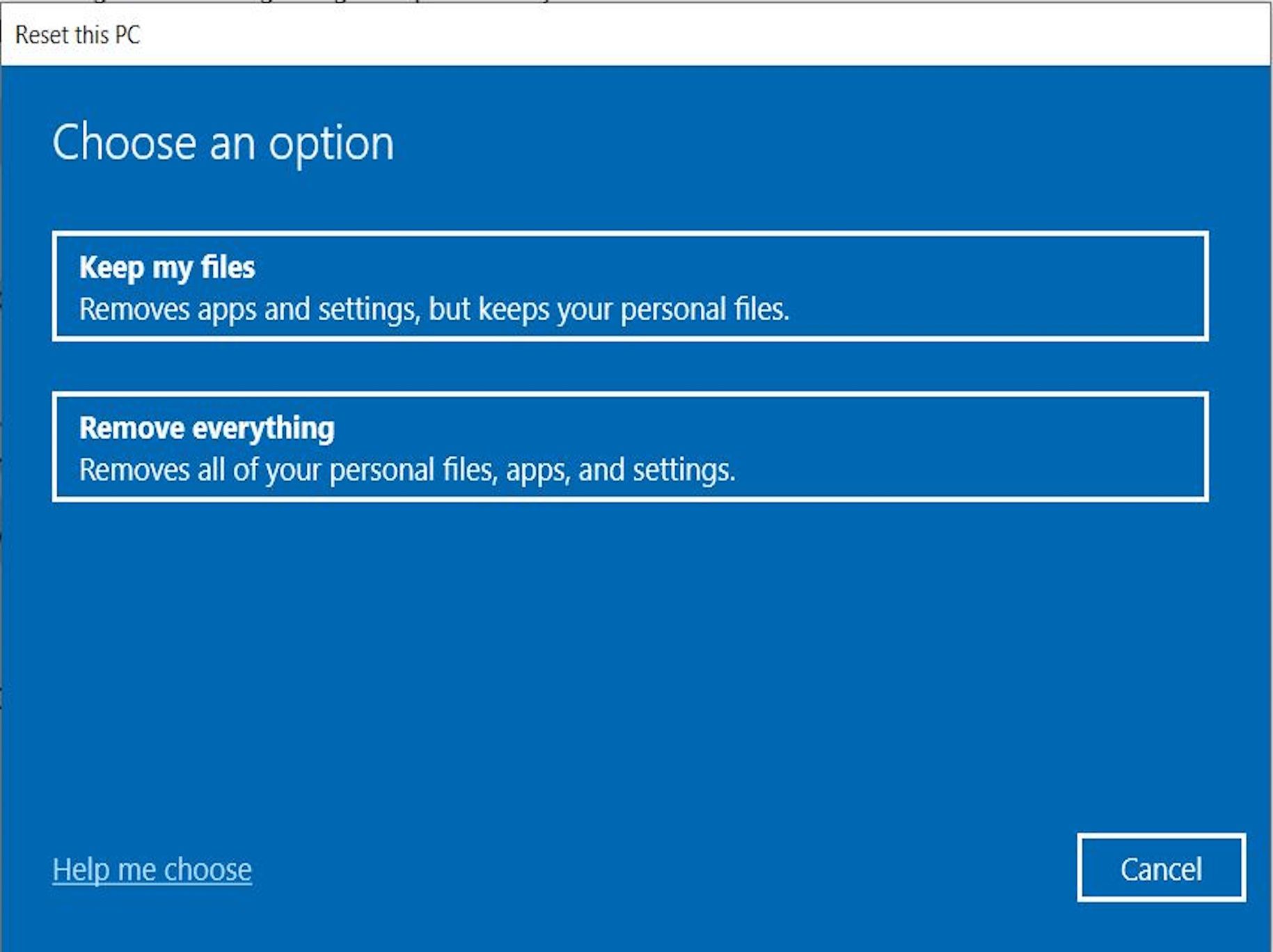
Reset Computer
You can reset your computer to a point (date and time) before the keylogger infection. This action will give you a fresh start, but will remove most of your apps, pre-installed desktop apps, antivirus software, digital licenses, and associated digital content. It is essential to ensure that important files and programs are backed up before resetting—and to be certain that a keylogger is not disguised as one of these.
To reset your Windows computer, press Windows key > Settings > Update and security > Recovery > Reset this PC > Get started > Keep my files or Remove everything.
Use Windows Security
The most popular operating systems, Windows and macOS, offer some level of threat protection. For instance, Windows Security (Defender) can scan your PC and remove viruses and other threats such as keyloggers. This is one of the best free antivirus programs.
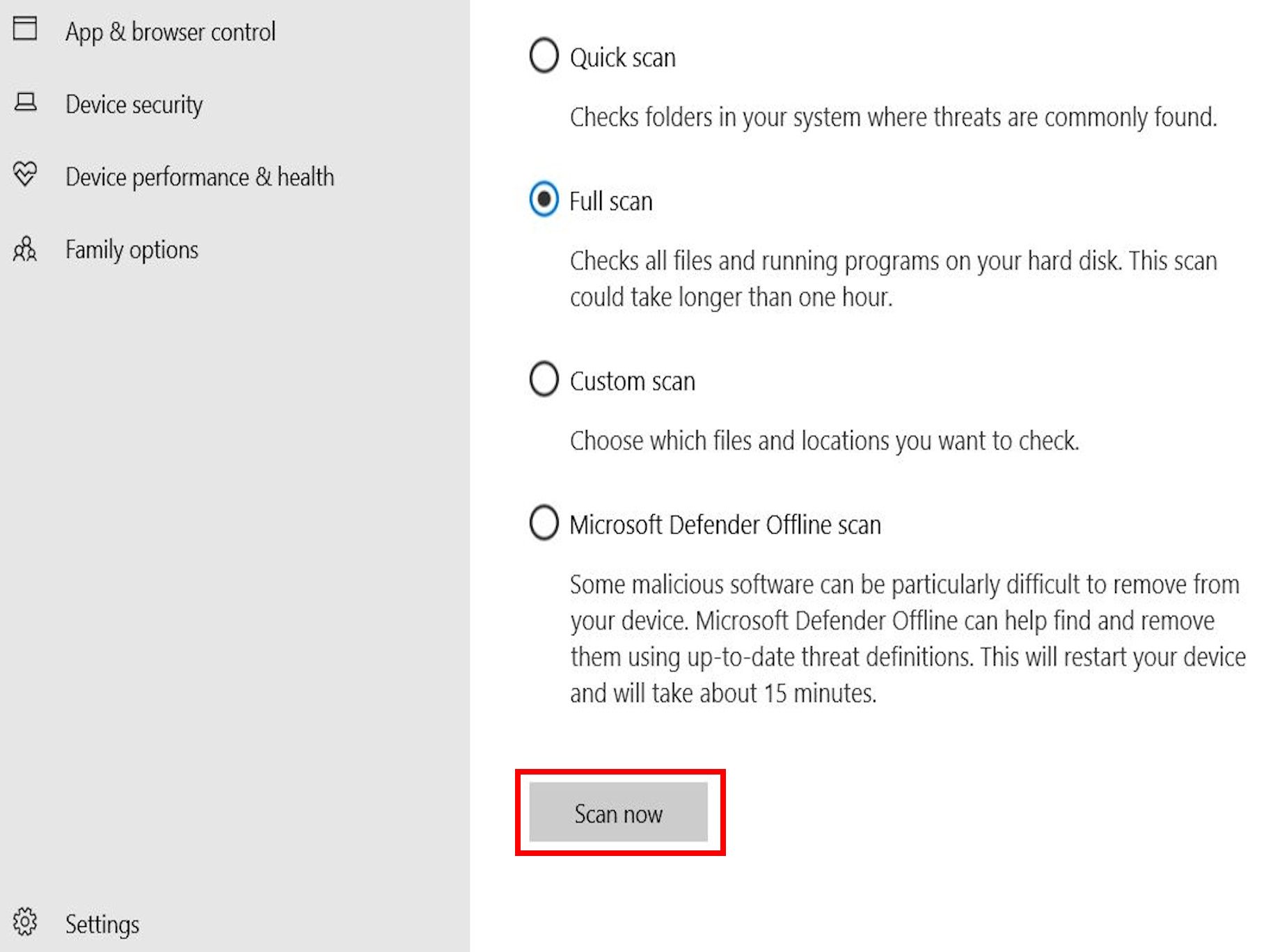
To remove keyloggers using Windows Security, press the Windows key > Settings > Update and Security > Windows Security > Virus and threat protection > Scan options > Full scan > Scan now. Then, remove any keyloggers or malware that is found.
Enable Microsoft Defender Offline Scan
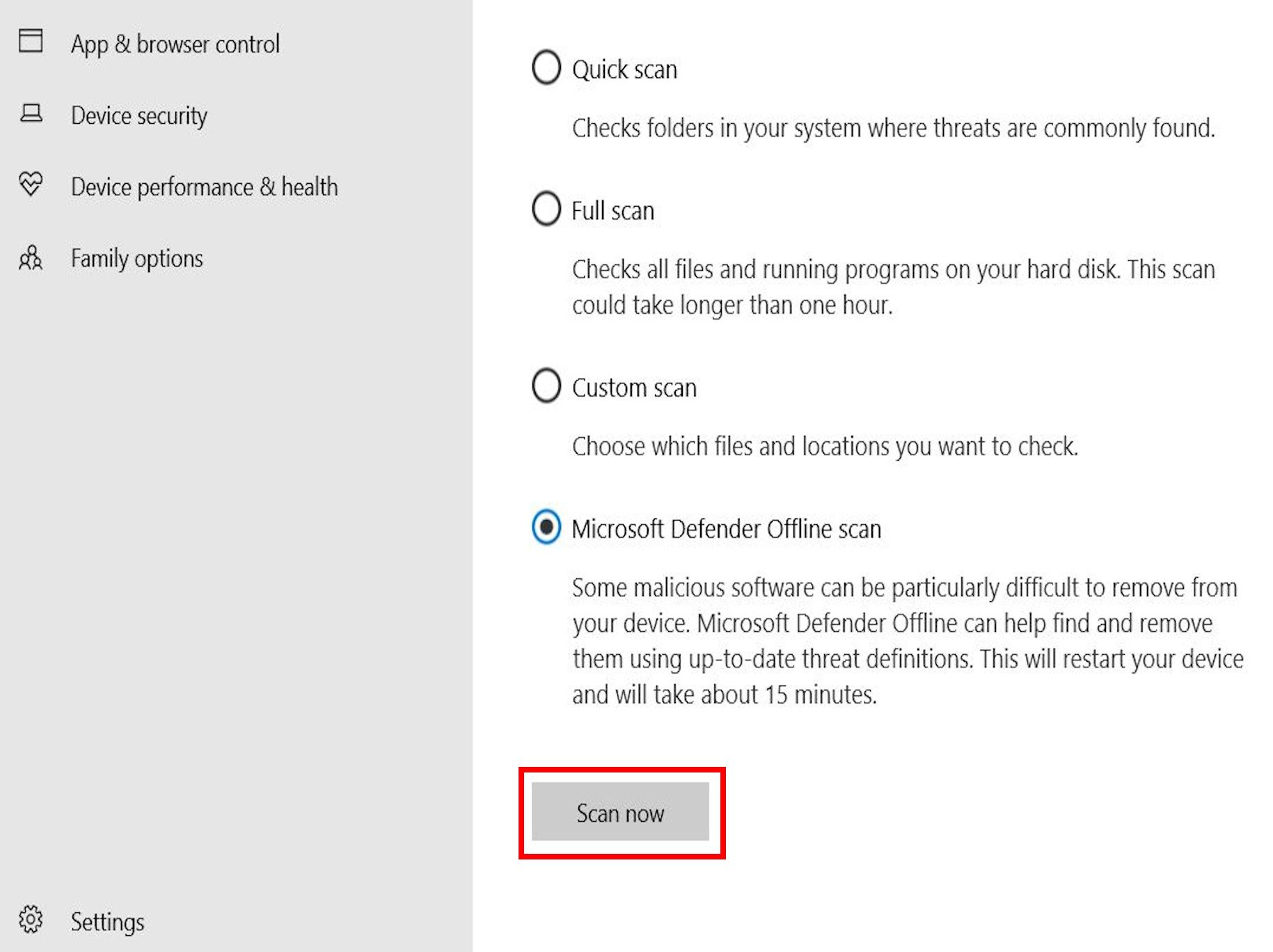
Microsoft Defender Offline Scan scans your PC for malicious software such as keyloggers and automatically removes them even when you’re offline. It is quick and easy to set up.
To enable Microsoft Defender Offline Scan, press the Windows key > Settings > Update and Security > Windows Security > Virus and threat protection > Scan options > Microsoft Defender Offline Scan > Scan now.
Use Dedicated Antivirus/Spyware Remover
If all else fails, a dedicated and robust antivirus or spyware removal tool can help to remove keyloggers from your device. There are many options to choose from. Some of the most popular include Bitdefender, Kaspersky, Norton, and McAfee.
How to Protect Yourself From Keyloggers
As the saying goes, an ounce of prevention is worth a pound of cure. Proactively preventing keylogger infection is much easier than removing keyloggers. Consider taking the following steps to protect yourself from keylogging attacks.
| Action | Description |
| Stay informed | Understand and stay up to date on keyloggers, their characteristics, the ways they operate, symptoms of keylogger attacks, and necessary countermeasures. |
| Monitor devices | Never leave personal or company-issued devices unattended or in places where unauthorized persons can access them and introduce keyloggers. |
| Move devices away from CCTV | Move devices away from CCTV, as threat actors can replay footage to capture keyboard input or keystroke patterns entered by users. |
| Lock devices | Lock your devices when not in use. Set up a PIN/password and minimize Sleep/Hibernate intervals. |
| Supervise contractors | Always supervise external IT contractors who have access to your company’s IT infrastructure to prevent malicious actors from installing keyloggers. |
| Inspect hardware | Routinely inspect your devices for hardware keyloggers, paying attention to USB-PS/2 ports and keyboard internals. |
| Download with caution | Most software keyloggers are contracted through malicious downloads. Avoid cracked or pirated software. Only download software or files from trusted sources. |
| Beware of email links and attachments | Email links and attachments from unknown sources are red flags, they can contain keyloggers. Double-check suspicious messages from known contacts to eliminate phishing, spear-phishing, or impersonation. |
| Use ad blockers and pop-up blockers | Ad-blockers and pop-up blockers do not directly prevent keylogging. However, they can block malicious scripts and prevent site redirects to malicious websites distributing keyloggers. |
| Try keystroke encryption | Keystroke encryption prevents keyboard inputs from being intercepted by keyloggers. It encrypts keystrokes with a military-grade cryptographic algorithm that can only be decrypted by the operating system or the receiving application. |
| Use auto-fill | Enable auto-fill in your browser settings so web forms fill automatically with a single click, without typing or tapping the keyboard. |
| Practice good password hygiene | Use password managers to skip typing usernames and passwords for keyloggers to steal, but be wary of browser extension versions. Do not reuse or repeat passwords, and update your passwords regularly to invalidate any stolen passwords. |
| Enable authentication and log-in alerts | Enable two-factor authentication (2FA), one-time passwords (OTP) and log-in alerts. They can alert you to unauthorized access by hackers using details obtained via keylogging. |
| Update operating system | Regularly updating your operating system, software, apps, and programs patches vulnerabilities protecting you from existing, evolving, and emerging threats, including keylogging. |
| Enable Virus and threat protection in Windows | Press Windows key > Settings > Update and Security > Windows Security > Virus and threat protection > Virus and threat protection settings > Manage settings, then turn on real-time protection, cloud-delivered protection, automatic sample submission, and tamper protection. |
| Use strong antivirus | A robust antivirus, anti-keylogger, or anti-spyware can detect, remove, and protect against most keyloggers. |
Protect Yourself With Gcore’s Web Application Security
Gcore protects against zero-day attacks and the OWASP Top 10. Zero-day attacks exploit previously unknown software vulnerabilities that may be used to deliver malware such as keyloggers. The same applies to OWASP Top 10 vulnerabilities, such as injecting or cross-site scripting.
Gcore’s advanced Web Application Security solution utilizes machine learning and real-time monitoring to scan and filter incoming traffic. It protects your assets against zero-day attacks and OWASP Top 10 attacks that can be used by attackers to deliver malware which may contain keyloggers.
Conclusion
When used ethically, as in parental or employee monitoring, keyloggers can be helpful. However, when used maliciously to steal sensitive data, keylogging attacks represent a major vulnerability, especially for enterprises that enable remote work from a range of devices. You can take steps to protect against and remove keyloggers yourself, but sometimes extra help is required.
With Gcore’s Web Application Security solution, your critical assets are protected against all forms of OWASP Top 10 and zero-day attacks that can be exploited to deliver malware which may include keyloggers.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.