Ransomware is present in 44% of all breaches, and in most cases, attackers steal your data before they encrypt it. Your bank login credentials can sell for up to $500 on the dark web within hours of being compromised. Here's the part that should concern you most: human error alone accounts for 26% of all breaches, meaning the biggest threat to your organization's data isn't an advanced hacker. It's an accidental email sent to the wrong person.
The risks are escalating fast. Attacks on edge devices and VPNs have increased nearly eight times as remote work expands, while phishing remains the most common attack vector, responsible for 16% of breaches. Stolen credentials can go undetected for up to 186 days, giving attackers nearly six months of silent access to your systems.
You'll learn exactly how data breaches happen, what makes your organization vulnerable, and the practical steps you can take to reduce your exposure before an incident forces your hand.
What is a data breach?
A data breach happens when unauthorized parties access or expose sensitive information your organization holds. It doesn't have to be an advanced hack. Human error alone accounts for 26% of breaches, while IT failures like misconfigured systems contribute another 23%.
Phishing is the single most common attack vector, responsible for 16% of incidents, and stolen credentials can go undetected for up to 186 days. The goal is almost always financial: stolen bank login credentials sell for as much as $500 on the dark web.
Why do data breaches happen?
Breaches happen because attackers, and honest mistakes, find gaps before you do. Human error alone accounts for 26% of breaches, from emailing files to the wrong person to misconfiguring cloud storage permissions. IT failures add another 23%.
Phishing is the most common attack vector, responsible for 16% of breaches. An employee clicks a convincing link, credentials get stolen, and attackers walk in through the front door looking like legitimate users — though threats like DDoS protection gaps can compound the damage when defenses are already stretched. Stolen credentials can take up to 186 days to detect.

How does a data breach happen?
Data breaches happen when unauthorized parties find a way past your defenses, and that path is more often human than technical. Human error accounts for 26% of breaches, from emailing files to the wrong person to misconfiguring a cloud storage bucket. Phishing drives another 16%, tricking employees into handing over credentials through convincing fake emails or websites.
Once attackers have a foothold, they move fast. Stolen credentials are especially dangerous because they're hard to spot. Legitimate-looking logins can go undetected for up to 186 days. IT failures add another 23% of incidents, mostly through outdated systems or overly permissive access settings that nobody noticed.
The attack pattern is usually the same: research your target, identify a weak point, then exploit it. That weak point might be a developer who left credentials in a public code repository, a vendor with poor security practices, or an employee who clicked the wrong link. Ransomware shows up in 44% of all breaches, and attackers typically steal your data before encrypting it, giving them double leverage.
What are the consequences of a data breach?
Data breach consequences range from immediate financial losses to long-term reputational damage that can take years to recover from. The main consequences are listed below.
- Financial losses: Breach investigations, legal fees, regulatory fines, and customer notifications all add up fast. Depending on the industry and jurisdiction, fines alone can reach millions of dollars.
- Regulatory penalties: Industries like healthcare and finance face strict data protection laws. A single breach can trigger investigations under regulations like GDPR or HIPAA, resulting in significant penalties.
- Reputational damage: Customers lose trust quickly when their data is exposed. Rebuilding that trust takes time, and some customers simply don't come back.
- Operational disruption: Ransomware is present in 44% of all breaches, and an attack can halt business operations entirely. Recovery often takes days or weeks, not hours.
- Intellectual property theft: Attackers target trade secrets, product roadmaps, and proprietary code. Losing this data hands competitors a direct advantage.
- Customer data exposure: Stolen personally identifiable information (PII) and credentials end up for sale on the dark web. Bank login credentials alone can fetch up to $500 per account.
- Legal liability: Affected customers and partners may pursue civil litigation. Class action lawsuits following large breaches have become increasingly common.
- Increased attack surface: Once attackers have valid credentials, they can move laterally through your systems. Stolen credentials take up to 186 days to identify, giving attackers extended access.
- Supply chain impact: If your systems are compromised, your customers and partners are at risk too. A breach in your environment can cascade downstream to everyone who trusts your infrastructure.
What are some notable data breach examples?
Some of the most damaging breaches in history share a common thread: they exploited gaps that organizations didn't know existed. Here are the ones security teams still reference today.
| Company | Year | Records exposed | Root cause | Data stolen |
|---|---|---|---|---|
| Yahoo | 2013–2014 | 3 billion accounts | Forged authentication cookies and stolen credentials | Names, email addresses, hashed passwords |
| Marriott International | 2018 | ~500 million guests | Undetected attacker access for 4 years via Starwood acquisition | Passport numbers, payment card data, contact details |
| Equifax | 2017 | 147 million people | Unpatched web application vulnerability | Social security numbers, financial data, addresses |
| Target | 2013 | 40 million cards | Third-party vendor compromise (HVAC supplier) | Credit and debit card numbers |
| 2012 | 117 million accounts | Poorly hashed passwords | Email addresses and passwords | |
| Colonial Pipeline | 2021 | N/A (operational disruption) | Single compromised VPN credential, no MFA | Ransomware — systems encrypted after data exfiltration |
| SolarWinds | 2020 | Thousands of downstream customers | Malicious code injected into a software update | Government and enterprise network access |
| Facebook / Cambridge Analytica | 2019 | 87 million users | API misconfiguration — overly permissive third-party access | Personal profile data harvested without consent |
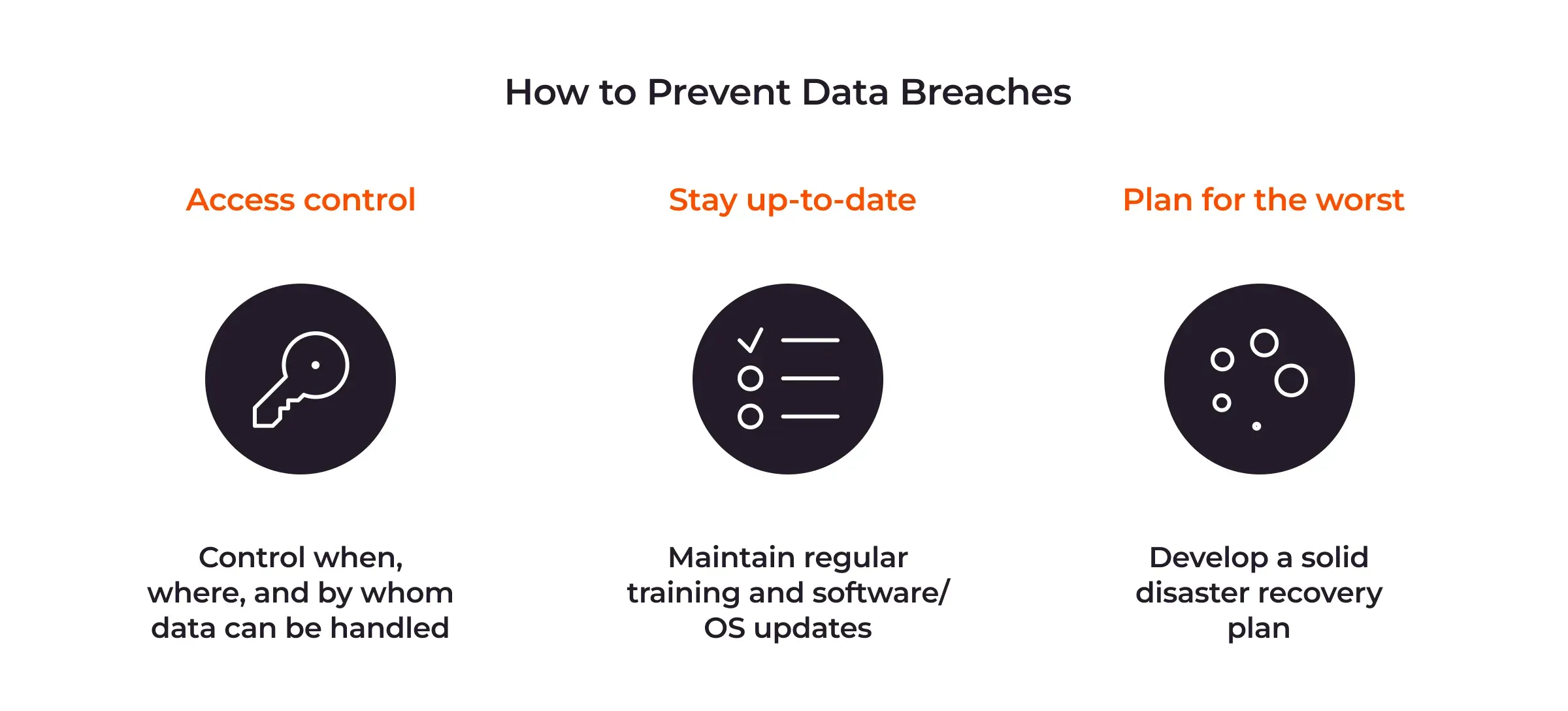
How to prevent a data breach?
You prevent data breaches by layering technical controls, employee training, and ongoing monitoring so attackers have fewer ways in and less time to go undetected.
- Train employees on phishing and social engineering. Human error causes 26% of breaches, and phishing accounts for 16% more. Run regular simulated phishing exercises, not just annual awareness sessions. When people recognize suspicious emails and links, you cut off one of the most common attack paths before it starts.
- Enforce multi-factor authentication (MFA) across all accounts. Stolen credentials account for 10% of breaches and can take up to 186 days to identify. MFA means a stolen password alone isn't enough to get in. Apply it to email, VPNs, admin consoles, and any SaaS tools your team uses.
- Audit your cloud and SaaS configurations regularly. Misconfigured storage buckets and overly permissive sharing settings create silent exposure risks. Check for publicly accessible databases, open sharing links in collaboration tools, and accounts with more access than they need. Most cloud breaches come from misconfigurations, not advanced hacking.
- Apply the principle of least privilege. Give users, contractors, and service accounts only the access they actually need to do their jobs. When someone leaves your organization, revoke access immediately. Insider threats, intentional or not, are far harder to detect when every account has broad permissions.
- Patch and update systems on a regular schedule. IT failures, including outdated and misconfigured systems, account for 23% of breaches. Attackers actively scan for unpatched vulnerabilities. Prioritize internet-facing systems, edge devices, and VPNs. Attacks on those have increased almost eight times as remote work has grown.
- Monitor for unusual behavior, not just known threats. Insider actions look legitimate, so they bypass traditional alerts. Deploy tools that baseline normal behavior and flag anomalies such as large file downloads, off-hours logins, or data moving to unapproved apps. Shadow IT and Shadow AI tools are particularly hard to catch without dedicated monitoring.
- Have a tested incident response plan ready. The faster you contain a breach, the less damage it does. Define clear roles, communication chains, and containment steps before an incident happens. A plan you've rehearsed works far better than one you're reading for the first time during a crisis.
The key thing to remember: no single control stops everything. Layering multiple defenses means that when one fails, others are still in place.
What should you do after a data breach?
There are clear steps you should take immediately after discovering a breach, and speed matters.
- First, contain the damage. Revoke compromised credentials, isolate affected systems, and disable any accounts that may have been accessed. Don't wait to confirm the full scope before acting. Every hour of delay gives attackers more time to exfiltrate data or cause further damage.
- Next, assess what was exposed. Identify which systems were affected, what data was accessed, and how the attacker got in. Stolen credentials can go undetected for up to 186 days, so your investigation needs to go deeper than the obvious entry points.
- Then notify the right people. Depending on your industry and location, you may have legal obligations to notify affected individuals and regulators within a specific timeframe. Delaying notification can turn a security incident into a compliance violation.
- Finally, fix the root cause, not just the symptom. If phishing triggered the breach, technical controls alone won't prevent the next one. You'll need to address the underlying vulnerability, whether that's a misconfiguration, a weak access policy, or a gap in employee awareness.
How can Gcore help prevent and respond to data breaches?
Gcore helps prevent and respond to data breaches through a layered security stack that covers your network edge, applications, and cloud infrastructure. Gcore's DDoS protection service, WAAP Service, API security, and bot management tools work together to help mitigate attack vectors such as credential stuffing, automated vulnerability scanning, and malicious bot traffic that contribute to breaches.
With 210+ Points of Presence globally, Gcore inspects and filters malicious traffic close to the source, keeping threats away from your origin before they can escalate. That matters when stolen credentials can take up to 186 days to identify through traditional monitoring alone.
Frequently asked questions
What is the difference between a data breach and a cyberattack?
A cyberattack is any malicious attempt to compromise a system. A data breach is what happens when that attack succeeds and unauthorized parties actually access or steal sensitive data. Not every cyberattack results in a breach, and not every data breach involves a cyberattack. Physical breaches and human error can cause breaches without any malicious cyber activity.
How long does it take to detect a data breach?
Stolen or compromised credentials take the longest to catch, up to 186 days on average, according to IBM's 2025 Cost of a Data Breach Report. Most breaches go undetected for weeks or months because attackers use valid login information that looks like normal user activity.
Who is legally responsible for a data breach?
Legal responsibility typically falls on the organization that collected and stored the breached data, not the attacker. Regulators under frameworks like GDPR and HIPAA can fine companies for failing to protect data, regardless of how the breach occurred.
What information is most commonly stolen in a data breach?
Attackers most commonly target personally identifiable information (PII), financial data, and login credentials. Bank account details alone can sell for up to $500 on the dark web. Healthcare records, trade secrets, and employee data round out the list, since they're all either directly monetizable or useful for follow-on attacks.
How much does a data breach cost on average?
The average data breach costs organizations $4.88 million, according to IBM's 2025 Cost of a Data Breach Report. Breaches involving stolen credentials take the longest to identify, up to 186 days, which drives costs even higher through extended exposure and remediation.
Can individuals take legal action after a data breach?
Yes, individuals can often take legal action after a data breach, depending on the jurisdiction and whether negligence can be proven. Class action lawsuits are common when large-scale breaches expose personal data, and some regulations such as GDPR give individuals the right to seek compensation directly.
What regulations govern data breach disclosure and reporting?
Data breach disclosure is governed by a range of regulations that vary by region and industry. GDPR in Europe, HIPAA for US healthcare, and state-level laws like California's CCPA each set their own notification timelines and requirements. Most mandate notifying affected individuals and regulators within 72 hours to 30 days of discovering a breach.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.






