Domain names are the entry point to online experiences, enabling effortless exploration of the digital realm. The Domain Name System (DNS) plays a crucial role by translating domain names (like www.gcore.com) into numerical IP addresses (like 92.223.84.84) for devices to connect with online destinations. However, cybercriminals can exploit DNS vulnerabilities. To fortify their online presence, organizations must implement robust DNS security measures. This article explores the significance of DNS security, how it works, and best practices that can help create a safer digital landscape.
What Is DNS Security?
DNS security refers to actions involved in protecting the Domain Name System infrastructure from cyberattacks, ensuring its reliable and efficient operation. One common attack is distributed denial-of-service (DDoS), where DNS servers are overwhelmed with excessive traffic, making it hard for legitimate users to access websites. Another vulnerability lies in the way DNS handles requests and responses. Attackers can manipulate source addresses and amplify their attacks, leading to a denial-of-service situation. DNS can also be abused through techniques like DNS hijacking, which means that users are tricked into connecting to malicious domains, or DNS tunneling, whereby cybercriminals use DNS requests to transmit data and evade detection.
To defend against these threats, organizations should adopt strong DNS security measures. This ensures the reliability, integrity, and confidentiality of their DNS infrastructure, protecting their online operations. Defensive measures employed to protect against potential threats include implementing redundant DNS servers and malicious traffic filtering, extending network capacity and leveraging anycast networking and geo distribution, employing security protocols like DNSSEC (Domain Name System Security Extensions,) and maintaining comprehensive DNS logging.
Why Is DNS Security Important?
The significance of DNS security cannot be overstated, considering the foundational role DNS plays in the functioning of the internet. Real-world incidents have demonstrated the exploitation of DNS vulnerabilities. For instance, some studies indicate that cybercriminals have used DNS attacks to steal sensitive data, resulting in substantial financial losses averaging $942,000 per attack. Application downtime affects 70% of organizations targeted in DNS attacks, highlighting their disruptive and financially damaging nature. Surprisingly, 43% of organizations still lack dedicated DNS security solutions, leaving them exposed to potential breaches.
Common Types of DNS Attacks

Understanding attack methods is crucial in implementing effective countermeasures to protect against such threats. Here are some common DNS attack methods:
- DNS spoofing: Attackers manipulate a DNS resolver’s cache, leading to misleading IP address responses and redirecting users to malicious replicas of legitimate websites used for malware distribution or credential harvesting.
- DNS tunneling: Attackers bypass firewalls by embedding malicious data within DNS queries and responses, using protocols like SSH, TCP, or HTTP to covertly transmit malware or stolen information.
- DNS hijacking: This involves attackers redirecting queries to unauthorized domain name servers using malware or unauthorized modifications, effectively altering the DNS record of a website and redirecting users to malicious destinations.
- Domain lock-up attack: Attackers establish TCP connections between specific domains and legitimate resolvers, flooding the resolver’s resources by sending slow streams of random packets, resulting in service degradation.
- NXDOMAIN attack: Attackers overload a DNS server with a barrage of requests for non-existent records, overwhelming its capacity and causing legitimate traffic to be denied access. Conversely, in a phantom domain attack, attackers establish unresponsive domain servers that flood the resolver with requests, impairing performance and leading to service disruption.
- Botnet-based CPE attack: By compromising Customer Premise Equipment (CPE) devices like modems and routers, attackers transform them into a botnet and unleash random subdomain attacks against specific sites or domains, causing disturbances and obstructing normal service operations.
Benefits of Implementing Robust DNS Security

DNS protection offers numerous security and performance benefits for both commercial and home networks. Implementing DNS protection strengthens security, enhances network performance, reduces the risk of malware infections, and protects against phishing attempts. It provides a holistic approach to network protection, benefiting both organizations and individuals by maintaining a secure online environment, which is extremely important, especially considering hybrid and remote work models.
Here are some less obvious advantages of implementing a secure DNS solution:
- Content filtering: Implementing secure DNS allows for content filtering without requiring additional software installations. It effectively blocks access to adult sites and unwanted content, reducing the risk of users inadvertently visiting malicious websites and consequently falling victim to cyberattacks.
- Advertisement blocking: Ad blocking is a subset of content filtering. Secure DNS solutions can effectively block advertisements that collect sensitive information or contain concealed malicious applications. By preventing the display of ads, system performance is enhanced, leading to improved employee efficiency and productivity.
- Botnet protection: With the increasing prevalence of IoT devices, botnets have emerged as a significant threat. DNS protection takes proactive measures to block communication with known botnet servers, thereby safeguarding devices from being compromised and enlisted in malicious activities.
- Malware and phishing blocking: Secure DNS solutions have the capability to block access to websites hosting potentially harmful or malicious content, including viruses and scams. Combining DNS security with proper training can significantly diminish the likelihood of individuals falling for phishing attempts.
- Enhanced speed and reliability: Secure DNS servers generally provide faster lookup times than DNS servers provided by internet service providers (ISPs.) This increased speed enhances overall efficiency and productivity. Secure DNS servers also offer heightened reliability, ensuring a smoother and more consistent internet connection experience.
- Enhanced lookup speed: Secure DNS servers generally offer quicker lookup times than ISP DNS servers. This is because secure DNS servers are equipped with advanced protection mechanisms and filters that may be lacking in ISP servers. As a result, users experience improved reliability and faster connection speeds, promoting greater productivity.
Now we understand the benefits of DNS security, let’s look at how it works in practice.
How Does DNS Security Work?

DNS security plays a critical role in safeguarding network operations by protecting against potential threats and ensuring the integrity of data exchanges. To understand the intricacies of DNS security and its underlying mechanisms, let’s break down how it works, step-by-step.
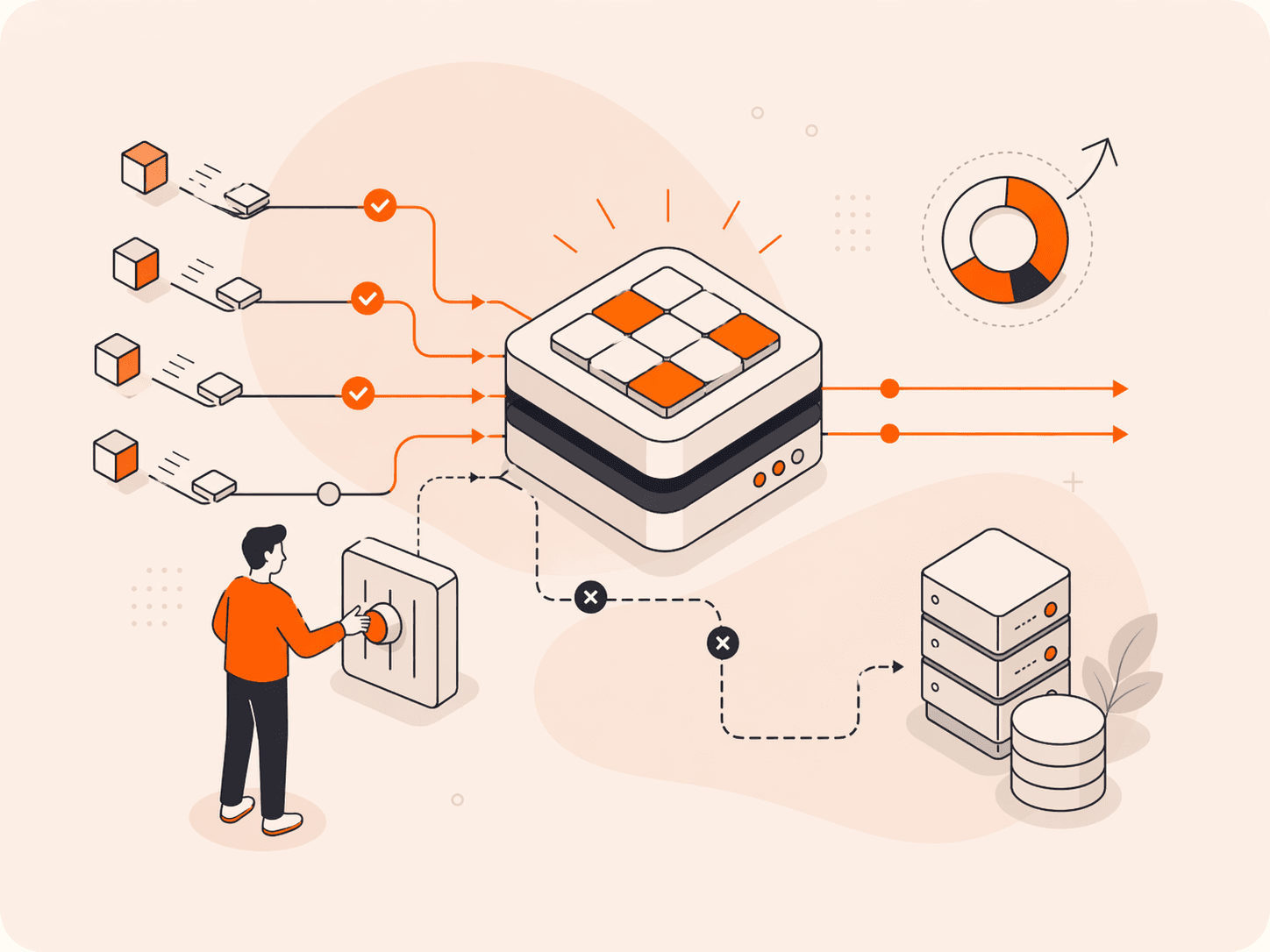
Step #1: Local Cache Check
When a user enters a domain name (e.g., www.petfood.com) into a web browser, the computer initially checks its local DNS cache for the associated IP address. If cached, the domain is served immediately. If the information is not found, the computer proceeds to perform a DNS query.
During the DNS lookup process, there are potential security vulnerabilities that can be exploited. One such vulnerability is DNS cache poisoning, where attackers manipulate or inject false DNS information into the cache, leading users to malicious websites. To mitigate this risk, security measures like DNSSEC (Domain Name System Security Extensions) can be implemented, ensuring data integrity and authenticity.
Step #2: Recursive DNS Server Query
In the absence of the IP address in the local cache, the computer sends a query to recursive DNS servers (resolvers). These DNS servers are designed to receive DNS queries from client machines through applications such as web browsers.
Recursive DNS servers can be susceptible to various security threats, including distributed denial-of-service (DDoS) attacks that aim to overwhelm the servers and disrupt DNS services. To mitigate these risks, security measures like rate limiting and traffic filtering can be implemented on the recursive DNS servers. Additionally, implementing secure communication protocols such as DNS over HTTPS (DoH) or DNS over TLS (DoT) helps protect the confidentiality and integrity of DNS queries and responses. (More on these measures later.)
Step #3: Recursive Resolver and Authoritative Server Query
When the IP address is not available in the recursive DNS server’s cache, the DNS server assumes the role of a recursive resolver. The resolver then searches for the authoritative DNS servers responsible for the specific domain. These authoritative servers store the DNS records associated with the domain.
During the discovery of authoritative DNS servers, attackers can attempt to hijack or spoof the responses from the recursive resolver, leading users to be redirected to malicious servers. To address this, measures such as DNSSEC, DNS source port randomization, and response validation can be implemented. These techniques help verify the authenticity of DNS responses and prevent DNS cache poisoning or redirection attacks.
Step #4: Retrieval of DNS Records
The recursive resolver sends queries to the authoritative DNS servers chain to obtain an answer (e.g., the IP address for the requested domain.) An answer is expected to be obtained from an authoritative server for this domain. And those servers are determined by recursive queries ( ask root NSs for .com NS servers, ask .com NSs for example.com NS servers, ask example.com NSs for www.example.com A record.) The authoritative servers respond with the IP address. Once the recursive resolver gets the IP address from the authoritative servers, it caches this address for future queries.
Security vulnerabilities that can arise during the retrieval of DNS records include Man-in-the-Middle attacks and DNS spoofing. To mitigate these risks, DNSSEC plays a crucial role by ensuring the authenticity and integrity of DNS responses. By validating the digital signatures attached to DNS records, a recursor can trust that the IP address received is legitimate and hasn’t been tampered with.
Step #5: DNS Configuration on the User’s Computer
The recursive DNS server provides the IP address to the user’s computer. The computer creates a local cache with the DNS record and retrieves the IP address. The web browser connects to the website using the obtained IP address from the DNS record.
Potential security vulnerabilities of an end user’s computer can include the manipulation of the local DNS cache or the interception of DNS responses. To enhance security, regular updates and patches should be applied to the computer’s operating system and DNS client software. Implementing secure DNS resolvers and using secure communication protocols like DoH or DoT on the user’s computer can also help protect against DNS-related security threats.
DNS Security Best Practices
Now we understand how DNS security works and recognize its importance, the need for businesses to prioritize and maintain smooth DNS operations is apparent. The rest of this article focuses on best practices. First, let’s explore a broad range of best practices, before diving into a few in more depth.
- Use DNS security extension/DNSSEC. Adopting a DNS security extension or DNSSEC adds an extra layer of security through the cryptographic authentication of DNS data. DNSSEC enhances trustworthiness by verifying the authenticity of retrieved DNS responses. Domain owners generate cryptographic keys and upload them to their domain registrar, reinforcing the integrity of DNS records. We’ll cover DNSSEC in depth in the next section.

- Get a DNS firewall. Employing a DNS firewall is another critical measure. Organizations can detect and block potential DNS attacks by directing visitor requests to an intermediary for analysis before reaching the authoritative nameserver. This ensures continuous operations even during attack scenarios.
- Conduct monitoring. Vigilant monitoring of DNS requests and subsequent IP connections significantly strengthens network security. Look out for signs of malicious behavior, such as unusual domain activity or attempts to spoof the DNS server. Identifying and promptly responding to unusual DNS activity allows businesses to proactively address malicious activities, compromised systems, and potential cybersecurity threats.
- Filter reported addresses. Organizations can configure their DNS servers to block requests associated with reported malicious websites and their associated IP addresses. Utilizing publicly available lists of such addresses enhances security protocols and helps mitigate risks.
- Configure in a segregated environment. Configure DNS servers in a segregated environment, limiting connections between servers and minimizing the impact of a compromised server.
- Update regularly. Keep DNS servers up-to-date with scheduled updates to introduce new security protocols and fix vulnerabilities promptly.
- Offer training. Provide comprehensive training to DNS server users, covering SSL/TLS certificate verification, cautious behavior with unrecognized links, and prompt security checks.
- Enable DNS logging. Recording and monitoring all DNS transactions allows network administrators to identify potential threats before they can compromise computer systems.
Let’s look at the first of these best practices in more depth.
What Is DNSSEC? What Does DNSSEC Do?
DNSSEC is a solution that significantly enhances DNS security. DNSSEC adds an extra layer of security by protecting against attacks like DNS cache poisoning, where attackers inject falsified data into DNS caches so that the DNS server stores and provides incorrect website addresses. DNSSEC checks the digital signatures and ensures that only DNS responses that have been signed and validated are accepted. This lowers the chances of you being directed to a malicious website and enhances the overall security of your internet browsing experience.
By implementing DNSSEC, organizations can also prevent DNS data from being compromised due to the inherent risk of a broken chain of trust introduced by untrusted or non-compliant resolvers. This is one of the major flaws associated with DNS.
DNSSEC incorporates cryptographic mechanisms to protect the integrity and authenticity of DNS data. Two key features of DNSSEC are the use of digital signatures and validation chains. Let’s explore how each works.
Digital Signatures
Imagine the DNS server as a trusted person, who signs their messages (in this case, the DNS data) with a special private key. When your computer receives this signed message, it can verify the authenticity of the message using a corresponding public key. In essence, the private key generates a digital signature, which is attached to the DNS data. This digital signature confirms that the data is genuinely from the DNS server and that it hasn’t been altered while being sent to your resolver.
Validation Chains
DNSSEC relies on a hierarchical chain of trust, where each level of the DNS hierarchy signs the data of its subdomains, creating a validation chain. Let’s break this down. The DNS has a hierarchical structure, much like a family tree but in reverse. At the top, we have the root domain, below that are top-level domains (like .com, .org), and under them are the individual domains (like “petfood” in “petfood.com.”) In DNSSEC, each level in this hierarchy signs the information of its subdomains, which creates a chain of trust or a validation chain.
During DNSSEC validation, the resolver verifies the digital signatures starting from the root servers, then top-level domain (TLD) and works its way down the chain, checking the digital signatures at each level until it gets to the specific domain you requested. This validation process guarantees the integrity of the DNS data and provides assurance that the information received is authentic.
Now, let’s look at another best practice for DNS security: DNS logging.
What Is DNS Logging? How Can It Help Promote DNS Security?
DNS logging involves the systematic collection of comprehensive data related to DNS traffic by recording and monitoring all DNS transactions handled by the DNS server. This process allows network administrators to observe and analyze the exchanged data during DNS resolution processes, aiding in the identification of potential threats before they can compromise computer systems. DNS logging plays a crucial role in identifying common types of DNS attacks, including DNS hijacking, DNS tunneling, and DoS attacks.
Once DNS logging is enabled, the DNS server starts generating log entries for each DNS transaction. These logs provide a chronological record of DNS activities, allowing administrators to review and analyze them for various purposes, such as troubleshooting DNS errors or identifying potential security threats.
On a micro level, by monitoring the data exchanged during DNS resolution, DNS logging enables the detection of malicious URLs, emails from phishing domains, command-and-control (C2) domains, or Typosquatting domains. DNS logs usually contain highly detailed information such as queried domain names, IP addresses, requested record types, and request flags, empowering administrators to verify known malware domains, identify compromised devices, and uncover signs of malicious activity.
By examining the DNS logs, administrators can gain insights into the network’s DNS traffic patterns, detect anomalies, and identify suspicious or malicious activities. They can also use the logged data to correlate events, track the source of attacks, and investigate security incidents. Different types of DNS logging, such as audit logging, analytical logging, and debug logging, offer varying levels of performance and impact on the DNS server.
We’ve now examined standard best practices in DNS security. However, two new practices are revolutionizing DNS security: DoH and DoT. Let’s look at them more closely.
What Are DoH and DoT? How Are They Revolutionizing DNS Security?
Emerging technologies are reshaping DNS security, paving the way for improved online privacy and data protection. Among these advancements are DNS over HTTPS (DoH) and DNS over TLS (DoT), two protocols designed to enhance security by encrypting DNS traffic and ensuring the authenticity of DNS requests and responses.
DoH
DoH, or DNS over HTTPS, operates by encrypting DNS queries within an HTTPS session, providing an additional layer of security by concealing DNS queries from unauthorized access. This encryption occurs through HTTPS sessions, minimizing the amount of information exchanged between users and servers. Major web browsers like Google Chrome, Microsoft Edge, and Mozilla Firefox have adopted DoH as part of their commitment to enhancing data privacy and security.
DoT
DoT, or DNS over TLS, encrypts DNS queries using the TLS security protocol. By applying TLS encryption on top of the user datagram protocol (UDP) used for DNS queries, DoT protects against tampering and on-path attacks, bolstering overall DNS security.
Comparing DoH and DoT
DoT and DoH each offer unique benefits. DoT safeguards DNS communication via encryption and allows network administrators control over DNS traffic, aiding in security policy enforcement and threat identification. Conversely, by camouflaging DNS traffic within HTTPS, DoH complicates third-party monitoring or manipulation of DNS queries, thus bolstering user privacy, especially in public Wi-Fi use or in places with internet censorship.
Choosing between DoT and DoH hinges on individual or organizational needs: DoT suits those prioritizing security control and policy enforcement, while DoH caters to those valuing privacy protection against unauthorized access or manipulation. The implementation of these technologies depends on factors such as DNS resolver support, client compatibility, and network infrastructure. A balanced approach to security and privacy may involve using both DoT and DoH simultaneously.
Conclusion
The vast amount of information available on the internet has unfortunately made organizations more vulnerable to DNS attacks. It is essential to take decisive steps to enforce and maintain DNS protection measures so that your organization is safe from DNS-related cybercrime.
By staying vigilant and taking advantage of reliable DNS protection solutions like Gcore’s DDoS protection solutions and enterprise dns hosting services, you can enhance your overall cybersecurity posture and protect your digital assets.
Get protected today with our free DDoS Protection trial.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.