Gcore Blog
Discover the latest industry trends, get ahead with cutting‑edge insights, and be in the know about the newest Gcore innovations.
Some AI jobs require the full power and predictability of dedicated bare metal clusters. Others need something more agile: compute that can be sized up or down quickly, used for a burst of experimentation, powered down when idle, and spun b
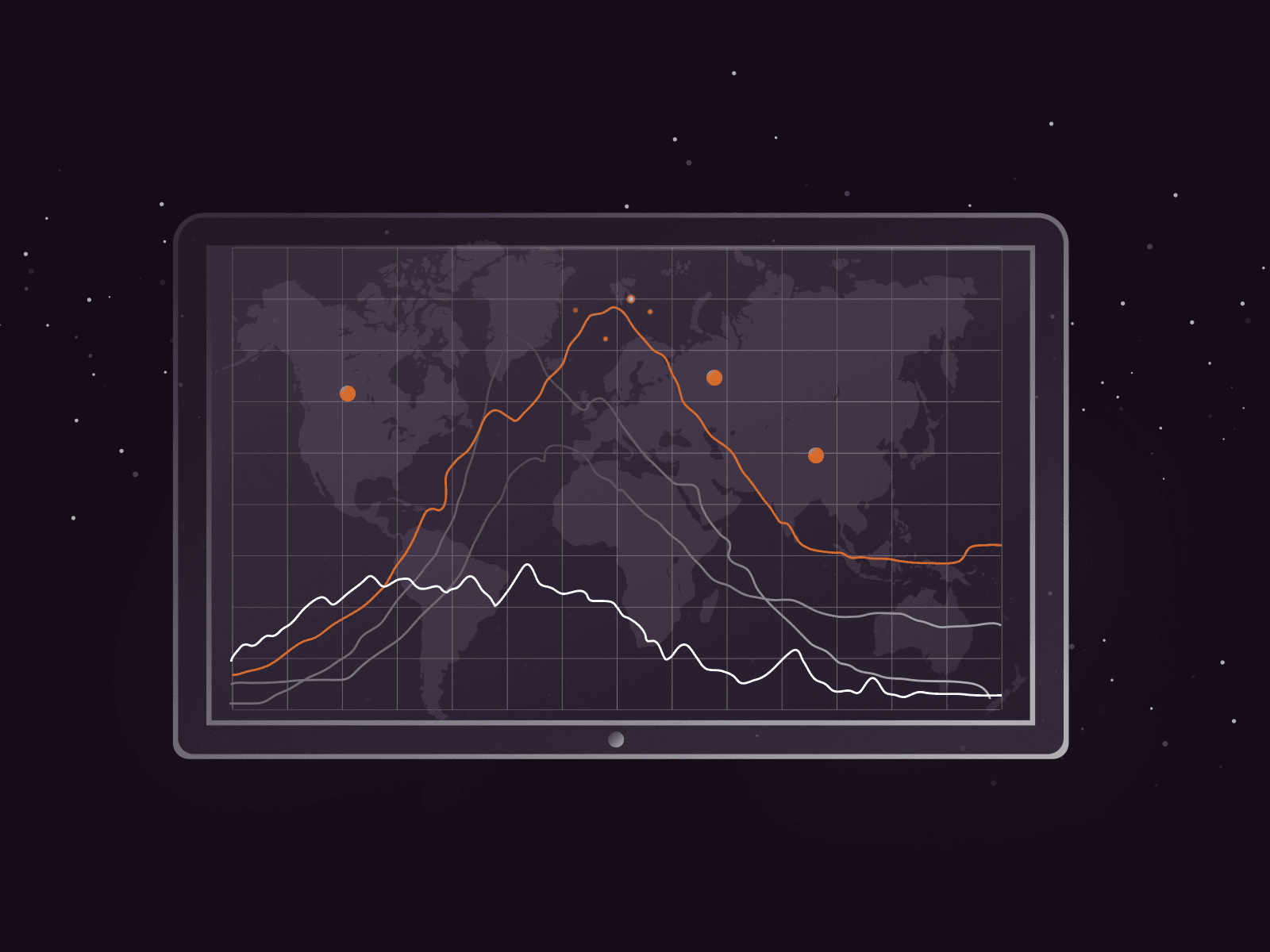
Cyberattacks are not just growing—they're accelerating at an alarming pace. The second half of 2025 marked a dramatic escalation in both the frequency and scale of DDoS attacks, with record-breaking volumes and increasingly sophisticated ta
AI adoption has a fragmentation problem. Organizations routinely stitch together separate tools for development, training, and serving, each with its own infrastructure, access controls, and operational overhead. The result is a patchwork t

E-commerce is moving fast — and the conversations at E-commerce Berlin Expo reflected just how much has changed in the last few years.Now that the event is over, here are four things I took away from speaking with key players across the ind
Three partnership announcements. One week. Twelve years in the making.Last week, as Gcore turned 12, we launched a new feature in partnership with NVIDIA and announced that Microsoft selected Gcore to join its elite group of global CDN part
Imagine if you could click a button and suddenly your GPUs increase their throughput by 6x. Or reduce latency by 2x. Or route inference requests seamlessly across different GPU types.That's the experience we're bringing to our inference cus
HLS/DASH streaming via CDN with ~3 seconds latency glass-to-glassLL-HLS and LL-DASH are well-documented standards, but delivering them reliably at scale is far from trivial. The challenge is not in understanding the protocols—it is in engin
We’ve expanded our AI inference Application Catalog with three new state-of-the-art models, covering massively multilingual translation, efficient agentic workflows, and high-end reasoning. All models are live today via Everywhere Inference
We’ve expanded our Application Catalog with a new set of high-performance models across embeddings, text-to-speech, multimodal LLMs, and safety. All models are live today via Everywhere Inference and Everywhere AI, and are ready to deploy i
For enterprises, telcos, and CSPs, AI adoption sounds promising…until you start measuring impact. Most projects stall or even fail before ROI starts to appear. ML engineers lose momentum setting up clusters. Infrastructure teams battle to b

At Gcore, delivering exceptional streaming experiences to users across our global network is at the heart of what we do. We're excited to share how we're taking our CDN performance monitoring to new heights through our partnership with AVEQ
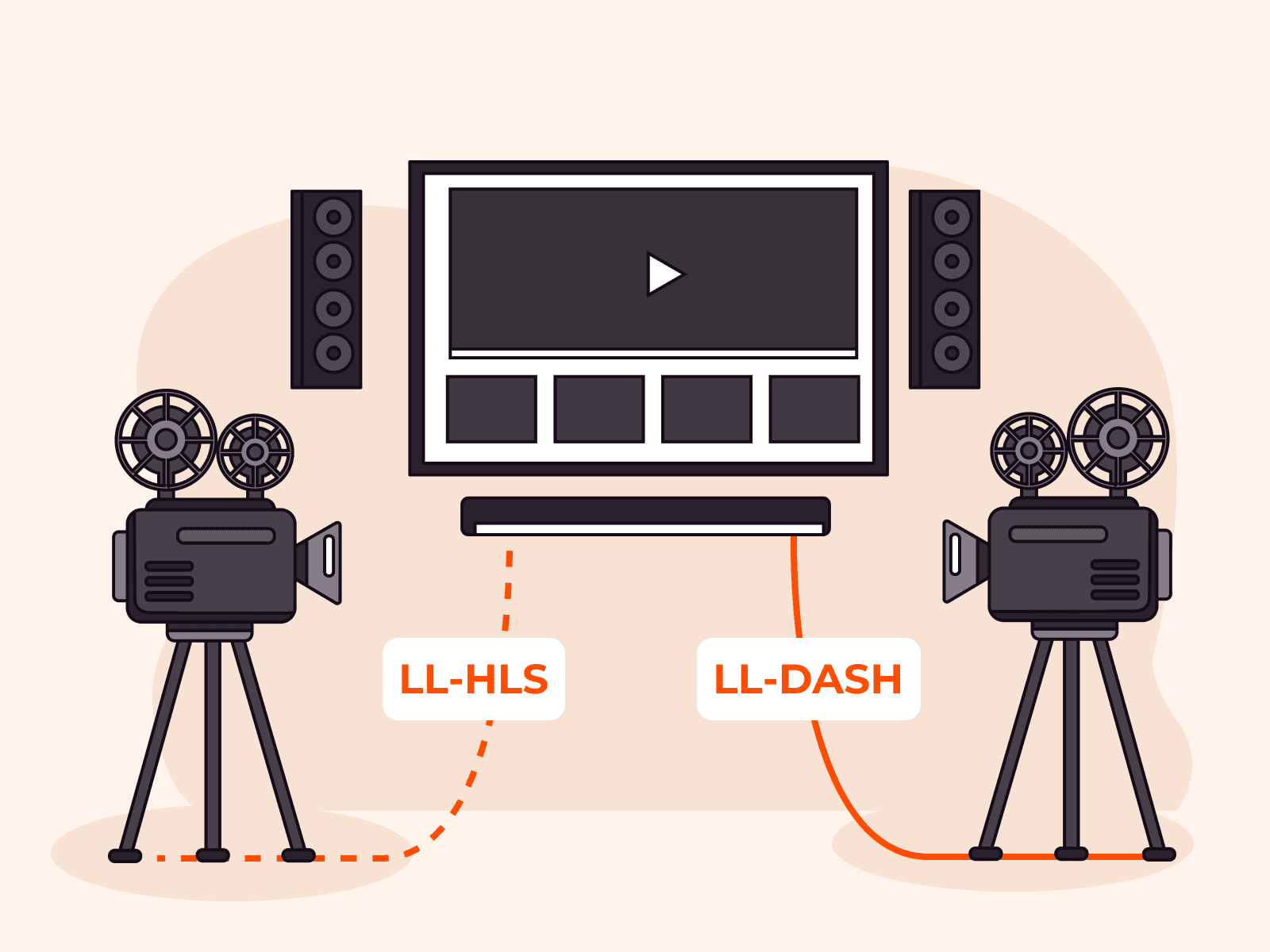
Viewers in sports, gaming, and interactive events expect real-time, low-latency streaming experiences. To deliver this, the industry has rallied around two powerful protocols: Low-Latency HLS (LL-HLS) and Low-Latency DASH (LL-DASH).While th
Gcore recently detected and mitigated one of the most powerful distributed denial-of-service (DDoS) attacks of the year, peaking at 6 Tbps and 5.3 billion packets per second (Bpps).This surge, linked to the AISURU botnet, reflects a growing
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.