DNSSEC (Domain Name System Security Extensions) is an extra layer of security for the DNS (Domain Name System) that ensures DNS requests aren’t spoofed. It provides cryptographic authentication to DNS data, which prevents users from being redirected to harmful web resources. This article explains why DNSSEC matters, what would happen without it, how it works, and how you can take advantage of it with Gcore to bolster your cybersecurity posture.
What Is DNSSEC?
DNSSEC is an extension to DNS protocols that adds a layer of security to the DNS (Domain Name System) lookup and exchange processes to protect against attacks such as DNS spoofing, man-in-the-middle, data modification, or cache poisoning, which involve an attacker redirecting queries to a different domain. DNSSEC introduces digital signatures to the DNS data to authenticate the origin of the data and verify its integrity while in transit.
Even though DNS has been at the heart of the internet for decades, it took two decades for DNSSEC to be introduced by IETF (Internet Engineering Task Force) two decades later than DNS itself. It started to be applied on a broad scale in the mid-2000s but still lacks universal uptake.
Why Was DNSSEC Invented?
DNS was designed for the smaller networks of the early 1980s, so it lacks a built-in means of security and, when used as-is, is vulnerable to serious flaws. DNSSEC was introduced to address a specific DNS security flaw—its weak authentication system—reinforcing it with digital signatures based on public key cryptography. There exist other DNS security mechanisms to address different specific DNS issues, detailed in our dedicated DNS security article.
Regardless of the scale and nature of your web business, without addressing the vulnerabilities in the original DNS implementation, you remain vulnerable to attacks. Implementing DNSSEC on your DNS server adds a reliable layer of security, verifying that all received DNS data originates from legitimate sources. This significantly reduces the vulnerability of businesses to cyberattacks and also helps to maintain their reputation as reliable partners and service providers.
Who Needs DNSSEC?
DNSSEC is important for any organization or individual that wants to ensure the security and integrity of their DNS data. This includes:
- Internet service providers (ISPs) who want to ensure their customers are directed to the correct websites and not malicious ones.
- Businesses with an online presence that want to protect their websites from being hijacked by hackers.
- Government agencies and other organizations that handle sensitive information and want to prevent data leaks and cyberattacks.
- Internet users who want to ensure that the websites they visit are genuine and haven’t been tampered with. (Individual users browsing the internet don’t have direct control over DNSSEC, but instead rely on the ISPs, domain owners, and DNS operators to implement and manage DNSSEC.)
DNSSEC is important for anyone interested in maintaining the trustworthiness and security of internet communications. Everyone—from government agencies and famous enterprises to family businesses and individuals—can contribute to the internet’s security by making choices that support the implementation of DNSSEC.
What Security Breaches Can Happen Without DNSSEC?
Without DNSSEC, serious cybersecurity breaches can occur. The two most common ways hackers exploit DNS security problems are as follows:
1. Spoofing. Attackers can intercept communications between a recursive resolver and an authoritative server, sending fake DNS data to the resolver while spoofing the IP address of the source packet. This redirects users to a potentially harmful web resource.
For example, users might be led to a page that pretends to be a bank website, which could then capture the user’s bank access credentials, or steal passwords to social media accounts. The potential for harm in such attacks is virtually endless.

2. Cache poisoning. Dan Kaminsky’s bug refers to a significant security vulnerability related to DNS caching. DNS uses recursive resolvers (essentially, servers) to store responses from authoritative servers in their cache, speeding up responses when the same request is made again. However, the downside is that these servers might end up caching forged or false responses.
This vulnerability can result in web cache poisoning. When multiple users request the same DNS data, they might all get served with the fraudulent information that was cached. This incorrect information could remain in the cache for the duration of the TTL (time to live) of the forged DNS data.
Modern precautions like request port randomization and source address rotation make this type of attack harder to carry out, but it’s still possible without DNSSEC. DNSSEC verifies the authenticity of the data’s source, ensuring that the information received is indeed from the claimed source, mitigating this vulnerability.
These examples only scratch the surface of the potential dangers web service owners face due to DNS vulnerabilities when they’re not using DNSSEC, especially in environments lacking other add-on layers of security technologies like HTTPS and IPsec.
Interestingly, these breaches are exploited not only by hackers but also by officials in some countries. For example, cache poisoning is a method used in the implementation of China’s “Great Firewall.”
How Does DNSSEC Work?
DNSSEC works by solving the two fundamental problems of DNS mentioned in the previous section.
- It authenticates the origin of the DNS data, ensuring that data is received from a legitimate source.
- It ensures data integrity by verifying that the data has not been modified in transit.
At a higher level, the DNSSEC specifications can be split into three processes that together achieve these two important protections: data authentication, signature authentication, and authenticated denial of existence.

1. Authentication of DNS Data
The owner of a DNS zone generates a public and private key pair. The private key signs the DNS data, while the public key is openly published. Recursive resolvers retrieve the public key along with the DNS data, using it to verify that the data was signed by the corresponding private key. The process is similar to how HTTPS works, with the difference that the private key is used only to sign data, not to encrypt it.

This scheme solves two critical problems: data authentication and integrity checking. If the signature verification is successful, the data is considered legitimate and forwarded to the user. Otherwise, the data is discarded, and the resolver responds with an error code, stopping the potential attack.
2. Authentication of Signature
After the authenticity of the digital signature is confirmed, how can you be sure that the public key used for verification is also genuine and wasn’t falsified as a result of a man-in-the-middle attack?
DNS zones are nested within each other hierarchically. The hash of the public key (DS) of one DNS zone is signed by the private key of its parent zone, and served from the parent zone. For instance, gcore.com’s hash of public key is signed by the com zone’s private key. This creates a “chain of trust”—a sequence of cryptographic keys each signed by another key. The public key of each DNS zone is authenticated by its respective parent zone’s key. The root zone, signed since July 2010, forms the first link in this chain and is widely trusted.

3. Authenticated Denial of Existence
If someone requests a non-existent domain address, the response can also be falsified in order to lead the user into opening an infected web resource. DNSSEC this threat with a technology called “Hashed Authenticated Denial of Existence.”
DNSSEC adds a record to DNS data called NSEC, which stores all existing domain names in the zone in lexicographical (alphabetical) order. When a DNS resolver queries a DNSSEC-protected DNS server for a record that doesn’t exist, the server responds with an NSEC3 record. This record essentially says “There’s no record by the name you asked for, and here’s a cryptographic proof to show that I’m not lying.” The end user will be shown an error message, and the falsified response won’t work.
DNSSEC Downsides
While DNSSEC significantly improves the safety of DNS-related network components, it’s not a complete solution: some security problems remain beyond its scope. While DNSSEC presents certain downsides—lack of protection on the last mile and confidentiality, and performance demands, which increase maintenance costs—its implementation is a valuable investment. The enhanced network security it offers, despite the associated complexities, is crucial in protecting your business against cyber attacks.
Last Mile Problem
One important aspect of DNSSEC implementation is that it resides on resolvers and is not able to verify data integrity from the resolver to the end user; the so-called “last mile.” Consequently, DNSSEC doesn’t protect the user if, for example, hackers break into their home network router and alter its DNS cache.

Lack of Confidentiality
This is not strictly a flaw, but DNSSEC doesn’t ensure user privacy. While it digitally signs and verifies DNS data, it does not encrypt it. This means a man-in-the-middle could still access a user’s DNS records. Other security protocols, like DNS-over-TLS and DNS-over-HTTPS, were designed to address DNS privacy concerns.

Performance Considerations
DNSSEC requires careful implementation with due consideration given to performance. The security mechanism consumes additional resources, and, unless properly managed, can lead to increased latency and decreased throughput.
The three primary ways DNSSEC can impact performance are:
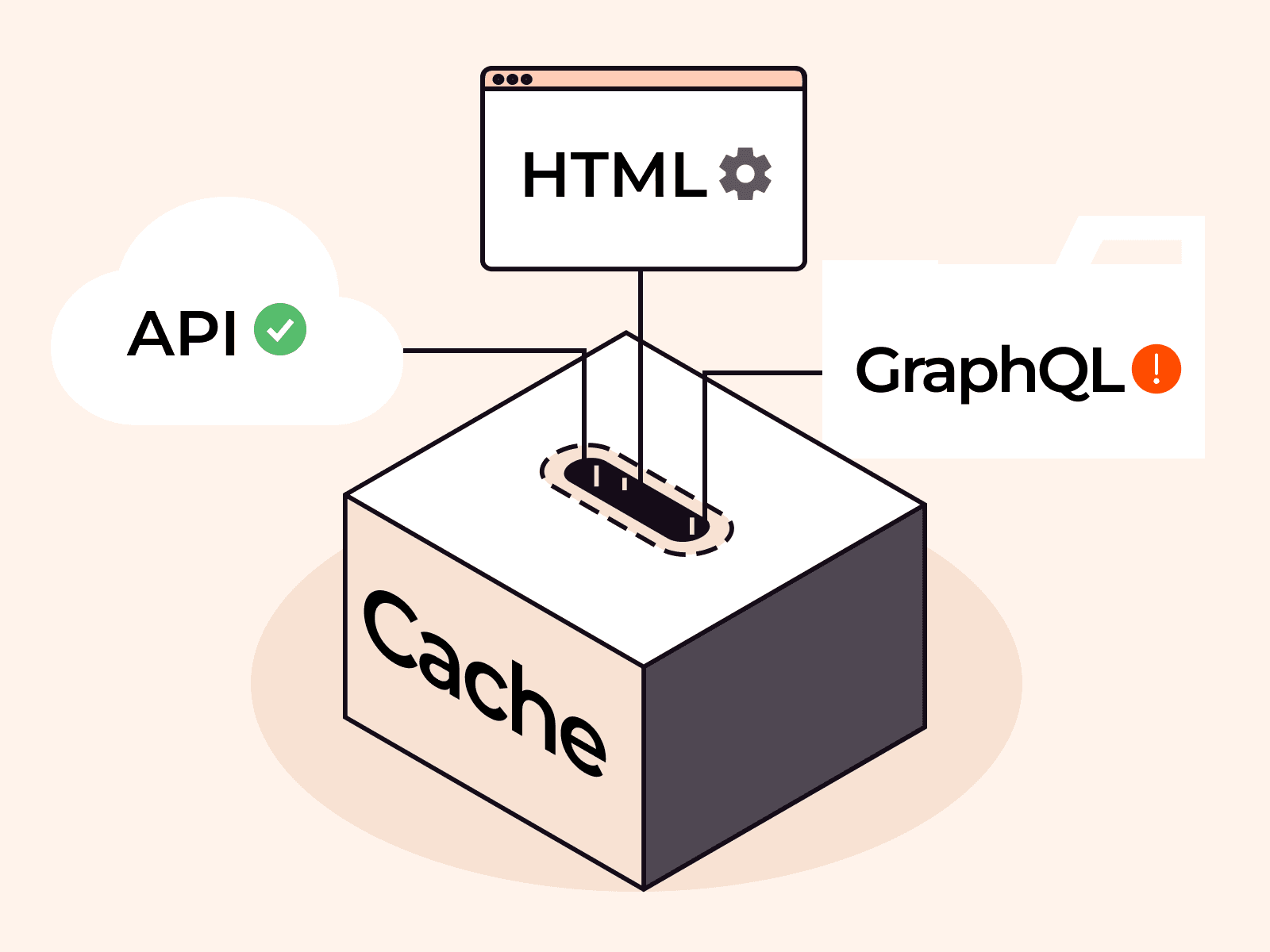
- Computational load: The implementation of DNSSEC involves key generation, data signing, and signature validation, all of which demand significant computational resources due to the intensive nature of cryptographic operations.
- Storage requirements: Compared to the DNS cache without DNSSEC, the system with DNSSEC enabled requires additional data storage because signed DNS data occupies more cache space, and public keys also require caching.
- Network traffic: DNSSEC increases network traffic because servers need to exchange cryptographic keys.
Together, these three factors impose additional hardware costs and increased maintenance demands.
How to Use DNSSEC with Gcore
Gcore’s DNS service alleviates the administrative burden of operating your own DNS server and provides essential security measures to counter DNS security vulnerabilities. It supports DNSSEC and also ensures that all recursive resolvers involved in domain resolution use DNSSEC. This comprehensive approach addresses every aspect of DNS security.
Don’t take Gcore’s approach for granted. For DNSSEC to work effectively, it must be implemented across all levels of DNS. While authoritative name servers now support DNSSEC, its overall adoption remains slow, and not all third-party DNS servers are compatible. Increased hardware requirements and maintenance costs can make managing a DNS server challenging. Choosing a provider with a thorough approach is essential for effective DNS security.
Conclusion
DNS is at the heart of the internet, which today means it’s a target for malicious cyberattacks that have the potential to cause serious financial and reputational damage. While it doesn’t guarantee complete DNS security, DNSSEC is one crucial element in securing the internet. While it’s widely recognized that secure networks depend on secure DNS, the slow adoption of DNSSEC suggests we’re still far from a fully secure internet.
Gcore implements DNSSEC at all DNS levels for comprehensive protection. Protect yourself from malicious actors who seek to redirect users to harmful sites and compromise or falsify your data with Gcore DNS. We offer a free-forever plan as well as advanced options, all based on our network of 160+ Anycast servers, strategically located on six continents for blazing-fast performance no matter where you’re located.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.