A Load Balancer is a tool used to sort incoming requests across your Virtual Machines to improve your infrastructure’s fault tolerance.Documentation Index
Fetch the complete documentation index at: https://gcore.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Step 1. Initiate Load Balancer creation
Go to your project, navigate to the “Load Balancers” in the “Networking” section and click Create Load Balancer.
Step 2. Set the region
Select a region for balancing.Step 3. Set computing configuration
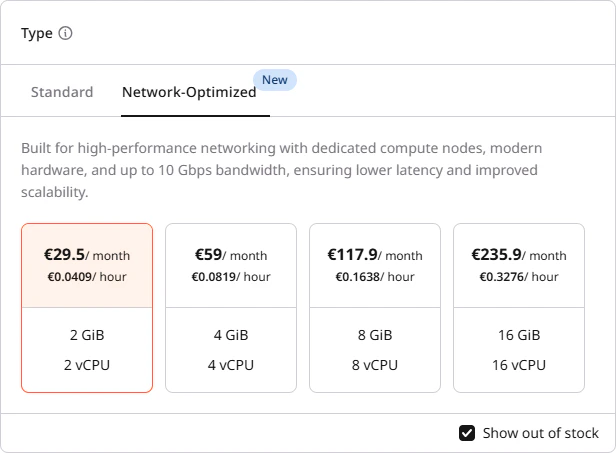
Select a suitable computing configuration for your Load Balancer: vCPU and GiB. All Load Balancers are created in high availability mode with active-standby instances. Upon failure of the active instance, the standby one will seamlessly take over the load-balancing functions.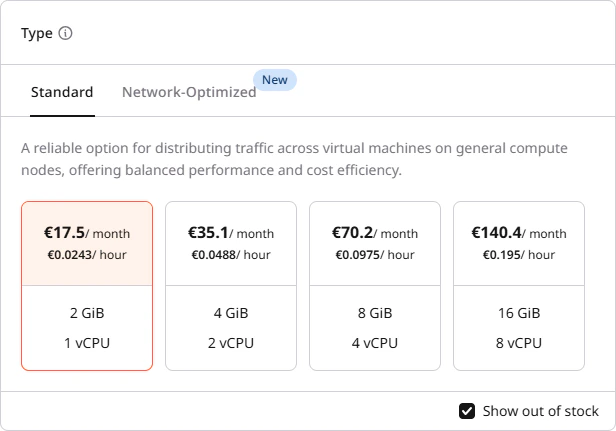
- Standard — general-purpose configurations suitable for most workloads, with network throughput up to 1.5 Gbps.
- Network-Optimized — built on network-optimised infrastructure with SR-IOV on the VIP port. These deliver significantly higher packet rates and lower latency, with guaranteed bandwidth up to 10 Gbps per instance.
| vCPU | RAM (GiB) | Network bandwidth (VIP) |
|---|---|---|
| 2 | 2 | 1.5 Gbps |
| 4 | 4 | 5 Gbps |
| 8 | 8 | 10 Gbps |
| 16 | 16 | 10 Gbps |
Step 4. Configure network
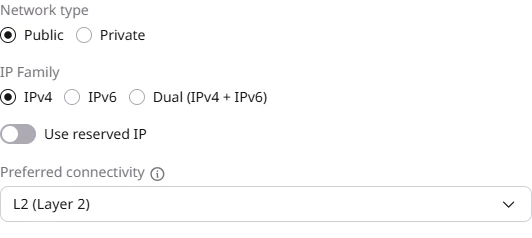
Configure the network interface:- Select the Network type: Public or Private.
- In the IP Family section, select the IP version: IPv4, IPv6, or Dual (IPv4 + IPv6).
- (Optional) Enable Use reserved IP to assign a reserved IP address to the Load Balancer.
- Configure Preferred connectivity (L2 or L3) as described in the next step.
Step 5. Configure preferred connectivity
You can choose between L2 (Layer 2) and L3 (Layer 3) connectivity. This setting determines the preferred connectivity method the Load Balancer uses to connect to backend pool members. If the preferred connectivity is not feasible, traffic will automatically route via the alternative method: L2 (preferred) → (if not possible) L3 → (if not possible) Validation Error L3 (preferred) → (if not possible) L2 → (if not possible) Validation Error The Load Balancer determines available routes only by evaluating subnet host routes. Due to current system limitations, it does not take routerhost_routes into account.
Layer 2
L2 connectivity offers better performance because traffic flows directly between the Load Balancer and pool members without passing through a router. This reduces network hops and minimizes latency. However, this approach requires more IP addresses. In networks with many/24 subnets, each Load Balancer must create ports in every subnet where its members are located. This can lead to high IP utilization and reduced efficiency in large-scale deployments.
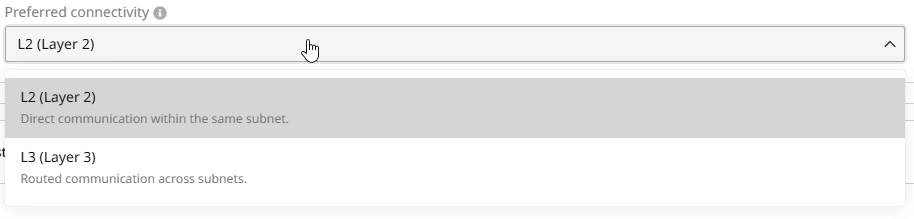
Layer 3
L3 connectivity routes traffic through a router or gateway, introducing additional network hops that may slightly impact performance. It also optimizes IP address utilization by reducing the number of required IPs per Load Balancer. Instead of allocating a separate IP in every subnet, the Load Balancer communicates with pool members across subnets using routing mechanisms. This approach improves scalability and efficiency, especially in environments with multiple subnets.Step 6. Configure listeners
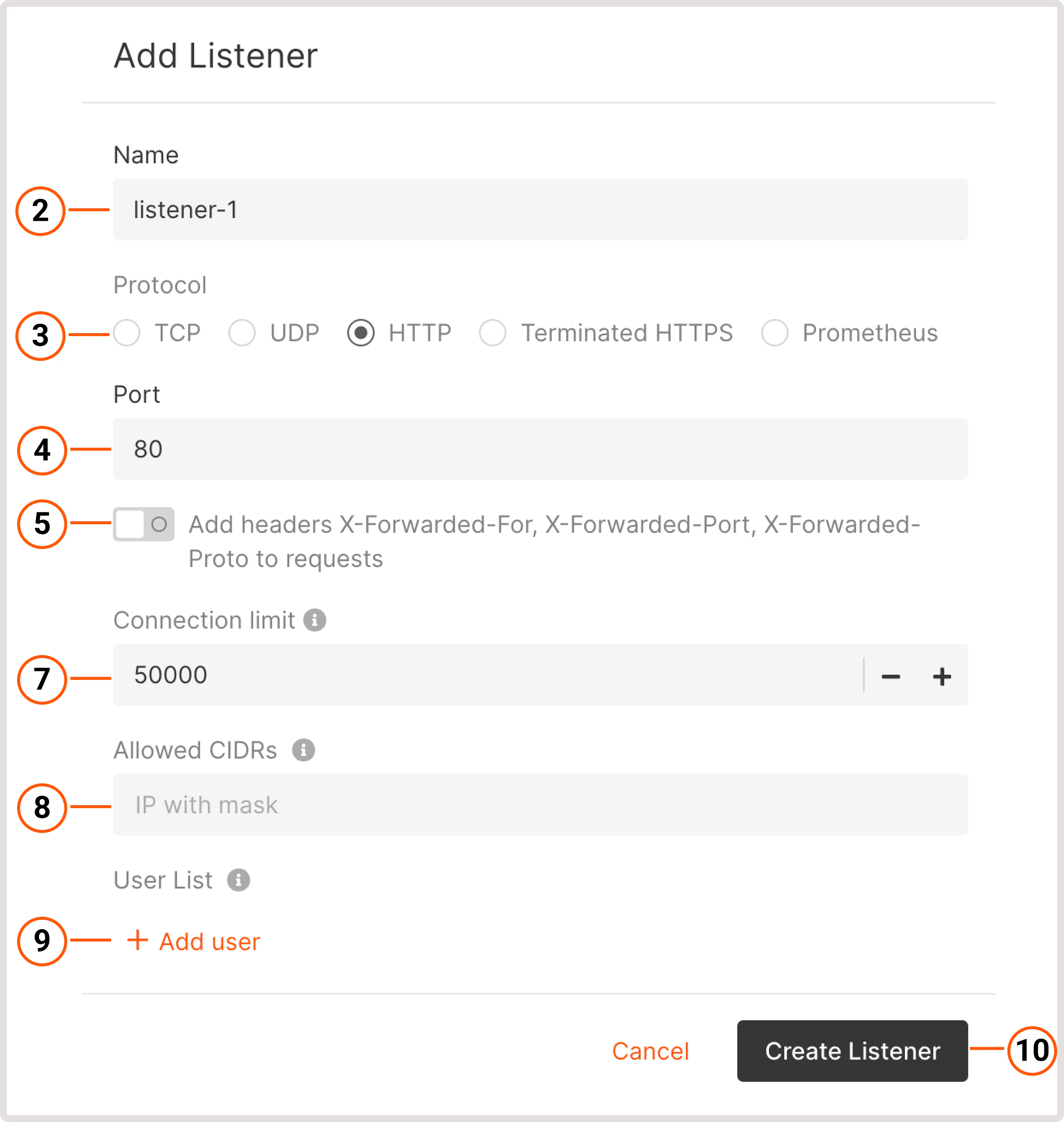
Add listeners that will check for connection requests using the protocol and port that you specify. You can add multiple listeners to a Load Balancer. To configure a listener:- In the Listeners section, click Add listener.
- Enter the listener’s name.
- Select the required protocol: TCP, UDP, HTTP, HTTPS, Terminated HTTPS, or Prometheus. You can configure multiple TLS certificates for Terminated HTTPS and Prometheus.
- Specify a port that the Load Balancer will listen on for incoming traffic. You can keep a default port for some protocols or specify the needed port from 1 to 65535.
- (Optional) To identify the origin of the user’s IP address connecting to a web server via a load balancer, enable the Add headers X-Forwarded-For, X-Forwarded-Port, X-Forwarded-Proto to requests toggle.
- If you select Terminated HTTPS and Prometheus protocols, you can configure TLS certificates. Follow instructions from our dedicated guide.
- Set the connection limit: the maximum number of simultaneous connections that can be handled by this listener. The default value is 100,000. Setting the value to -1 sets the limit to the default.
- (Optional) Add allowed CIDR ranges to define which IP addresses can access the content. All IP addresses outside the specified ranges will be denied access. Up to 100 CIDR ranges can be specified per listener.
- VIPs with both IPv4 and IPv6 support CIDRs of both versions.
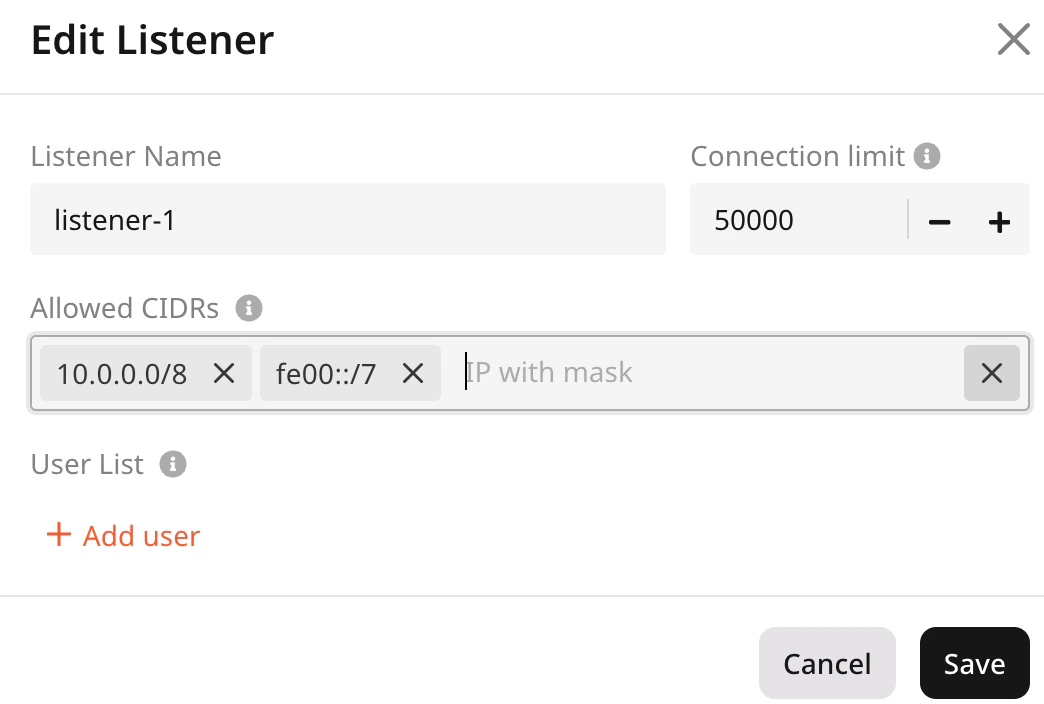
- VIPs with only IPv4 allow only IPv4 CIDRs
- VIPs with only IPv6 allow only IPv6 CIDRs
- (Optional) For HTTP-based listeners, you can configure basic user authentication to protect your resource from unauthorized access. Click Add users to enable the authentication:
- Enter username : specify a username.
- Password : specify a password or choose the Encrypted password option to store password as a hash. Check out create an encrypted password for instructions.
InfoA password must contain at least one lowercase character, one uppercase character, at least one number, and a special character. The maximum password length is 128 symbols.
- Click Create Listener.
Pool
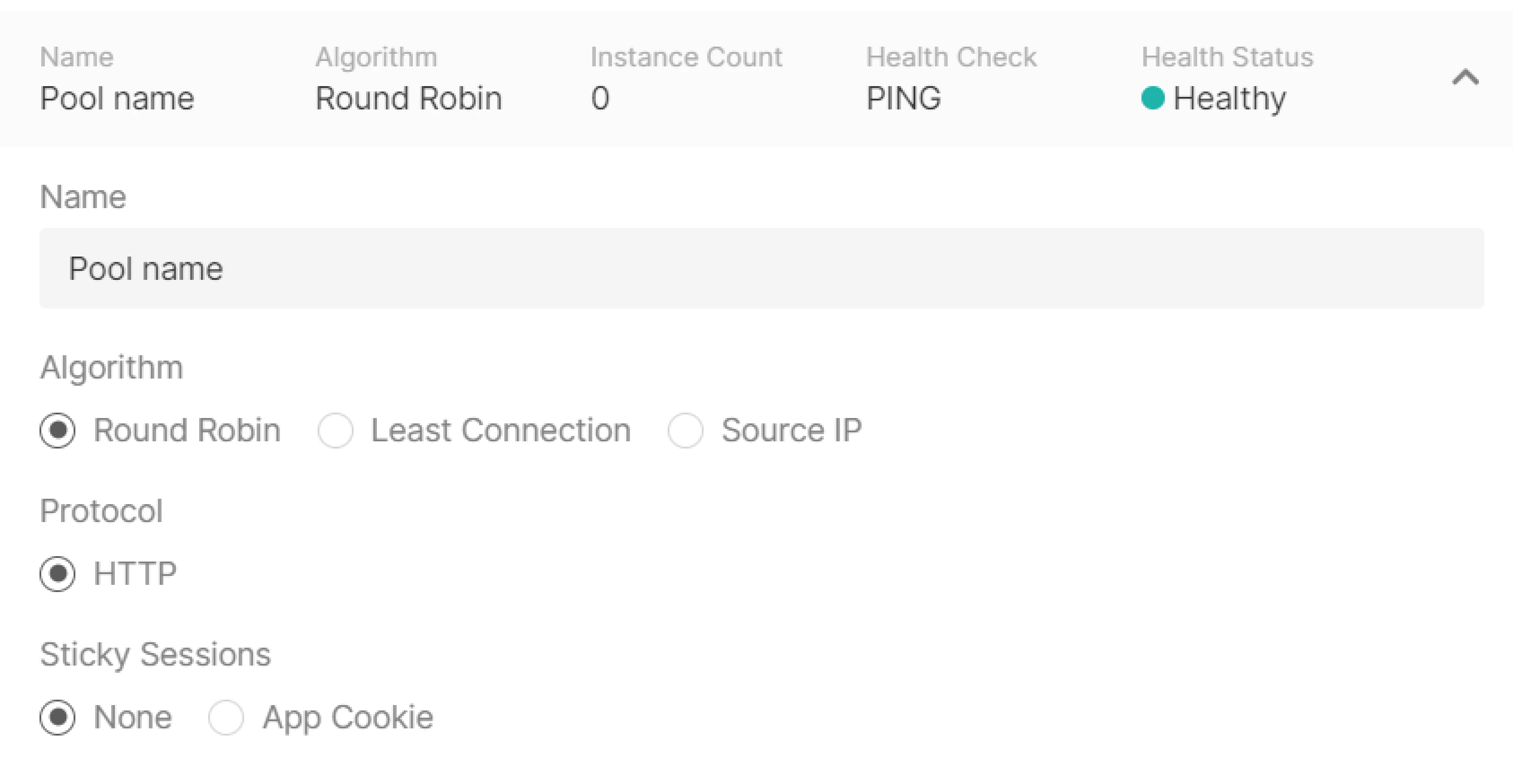
Configure a pool—a list of VMs to which the listener will redirect incoming traffic. Click Add new pool in the “Listeners” block to start configuring.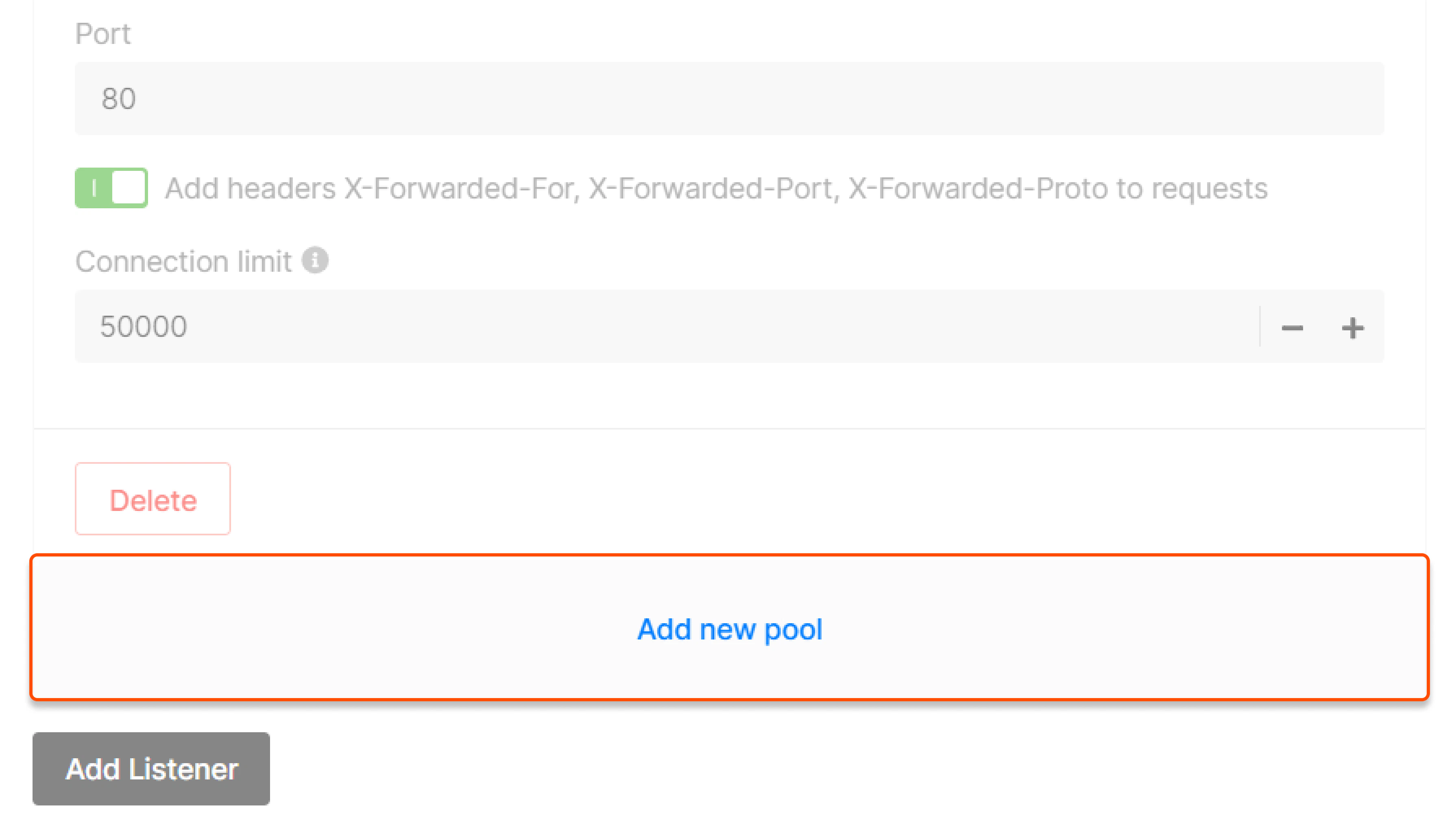
- Specify the pool name.
- Select the balancing algorithm:
- Round robin —requests are distributed across servers within a cluster one by one: the first request is sent to the first server, the second request is sent to the second server, and so on in a circle.
- Least Connection —new requests are sent to a server with the fewest active connections.
- Source IP —a client’s IP address is used to determine which server receives the request.
- Select a pool protocol—the protocol the Load Balancer uses to communicate with backend servers. The available options are: HTTP, HTTPS, TCP, PROXY, and PROXY V2. The pool protocol is independent from the listener protocol and should match what your backend application expects.
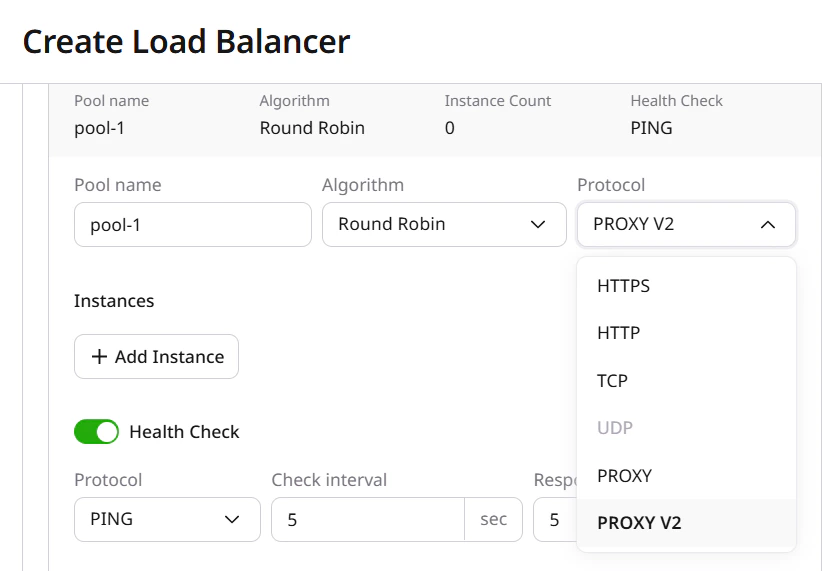
InfoPROXY and PROXY V2 require the listener to use the TCP protocol. Your backend application must be configured to parse Proxy Protocol headers. Selecting PROXY or PROXY V2 on a pool whose members do not expect these headers will cause connection failures.
- (Optional) Configure Sticky Sessions to route repeated requests from the same client to the same backend instance. In the Sticky Sessions dropdown, select the session persistence method:
- None — no session persistence, requests are distributed according to the selected algorithm.
- App Cookie — the Load Balancer uses an existing application cookie to route requests. Fill in the Cookie field with the cookie name. A special module creates a cookie and then uses it to forward requests to the same server.
- HTTP Cookie — the Load Balancer generates and manages its own session cookie automatically.
Instances

- Select Custom IP, Virtual Machine, or Bare Metal and the appropriate configuration.
- Specify the instance’s port and weight. Weight controls how much traffic is directed to each instance relative to others in the pool.
Health check
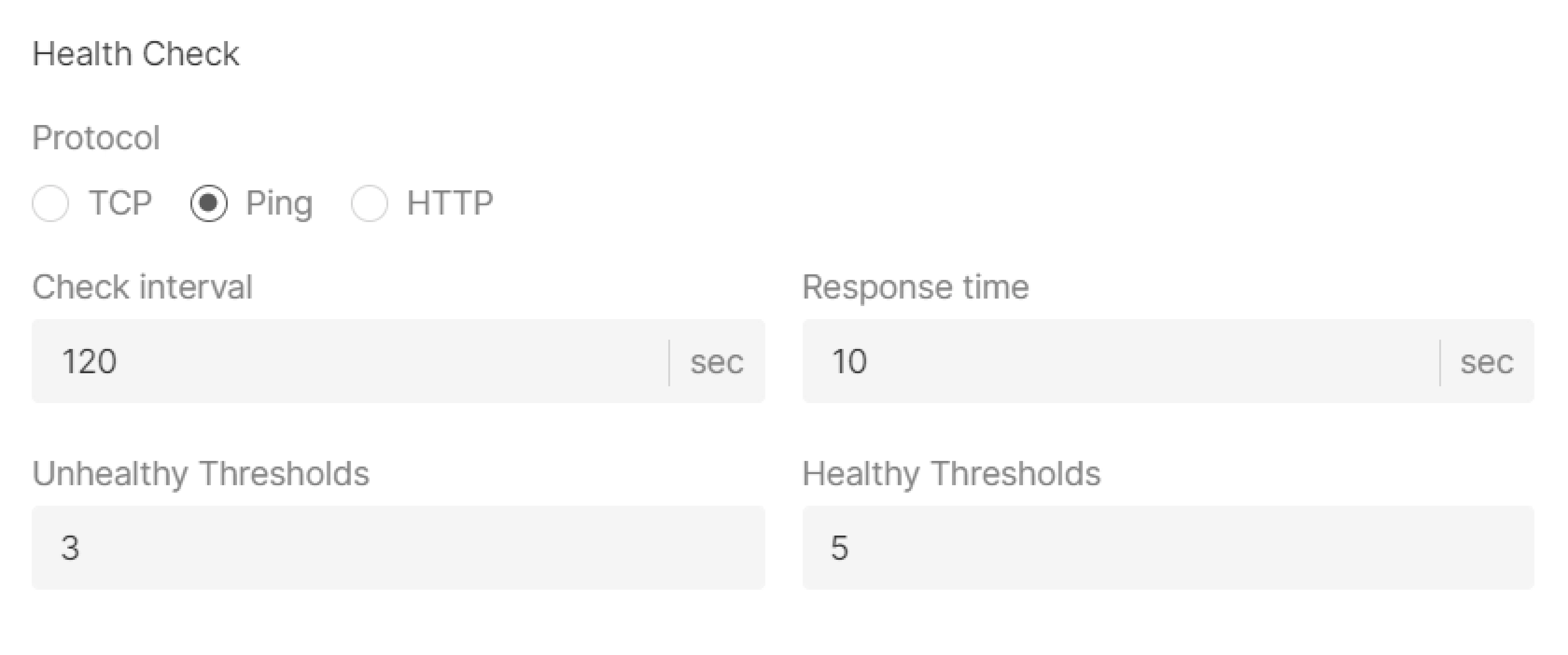
- Select the protocol for checking: TCP, Ping, or HTTP.
- Specify check interval (sec)—time between health check requests.
- Specify response time (sec)—the time to wait for a response from a server.
- Specify unhealthy threshold—the number of consecutive failed checks after which traffic will no longer be sent to the instance.
- Specify healthy threshold—the number of consecutive successful checks after which the instance will be considered ready to receive traffic.
Timeouts
Specify client data, member connect and member data timeouts in msec.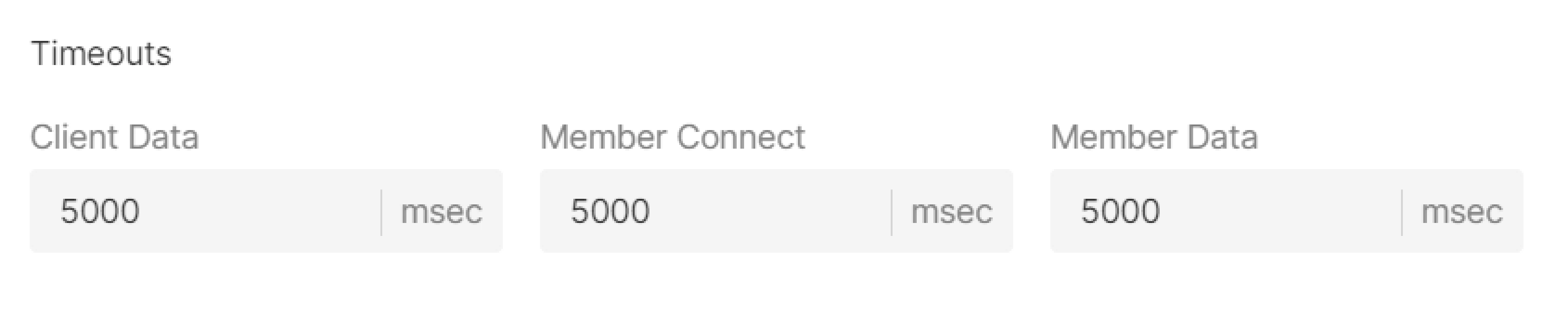
Sharing a pool across multiple listeners
A single pool can be used by multiple listeners within the same Load Balancer. This reduces configuration overhead and simplifies pool member management when routing traffic from different ports to the same backend servers.InfoShared pools can only be configured via the Load Balancer API.
- Create a Load Balancer via
POST /cloud/v1/loadbalancers/{project_id}/{region_id}. - Create a pool via
POST /cloud/v1/lbpools/{project_id}/{region_id}, specifyingloadbalancer_idwithoutlistener_id. - Create listeners via
POST /cloud/v1/lblisteners/{project_id}/{region_id}, referencing the pool viadefault_pool_id.
Step 7. Enter the name
Enter a name for the Load Balancer. This name will be displayed in the Gcore Customer Portal.
Step 8. (Optional) Enable logging
The Logging service will be activated to store your logs. To learn how it works and how to configure it, refer to the article about Logging.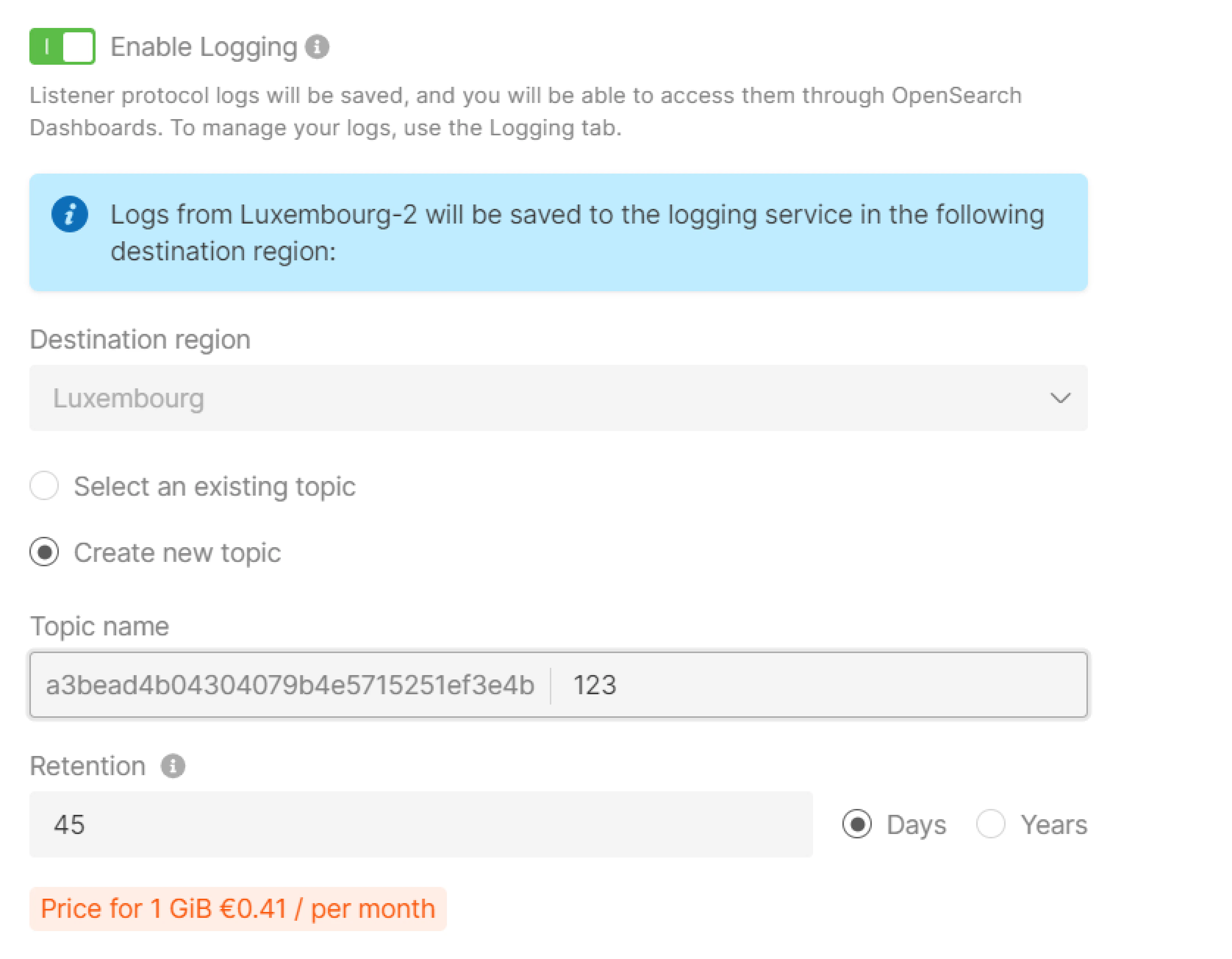
Step 9. (Optional) Add tags
Create tags for your load balancer by entering “Key” and “Value”.
Step 10. Finalize creation
Check the settings and click Create Load Balancer on the right.Step 11. Configure firewall
Configure firewalls for Virtual Machines in the pool according to the separate guide. Make sure their ports are open for the Load Balancer traffic:- If a Load Balancer and Virtual Machines are in a public network, set a rule to receive and transmit traffic to the balancer’s IP address (specified in the menu) in firewalls settings of the VM.
- If a Load Balancer and Virtual Machines are in a private subnetwork, set a rule to receive and transmit traffic to the entire private subnetwork or to the balancer’s IP address (specified in the menu).
- If a Load Balancer is in a public network and Virtual Machine are in a private subnetwork, set a rule to receive and transmit traffic to the entire private subnetwork or to the balancer’s internal IP address (send a request to the technical support).