Introducing New Real-Time DDoS Statistics Features
- October 10, 2023
- 2 min read

We are excited to announce the second part of our real-time DDoS statistics feature. Our customers can access invaluable real-time statistics directly, making it easier than ever to understand how we defend against threats. You no longer need to request a report and wait for access; instead, simply access your Gcore personal account on demand and get an instant look at how your project is being protected.
We recently announced the first part of DDoS statistics feature, and today we’re announcing the second part, which includes access to the following:
- 95 percentile value
- Minimum and maximum values for input dropped and passed traffic
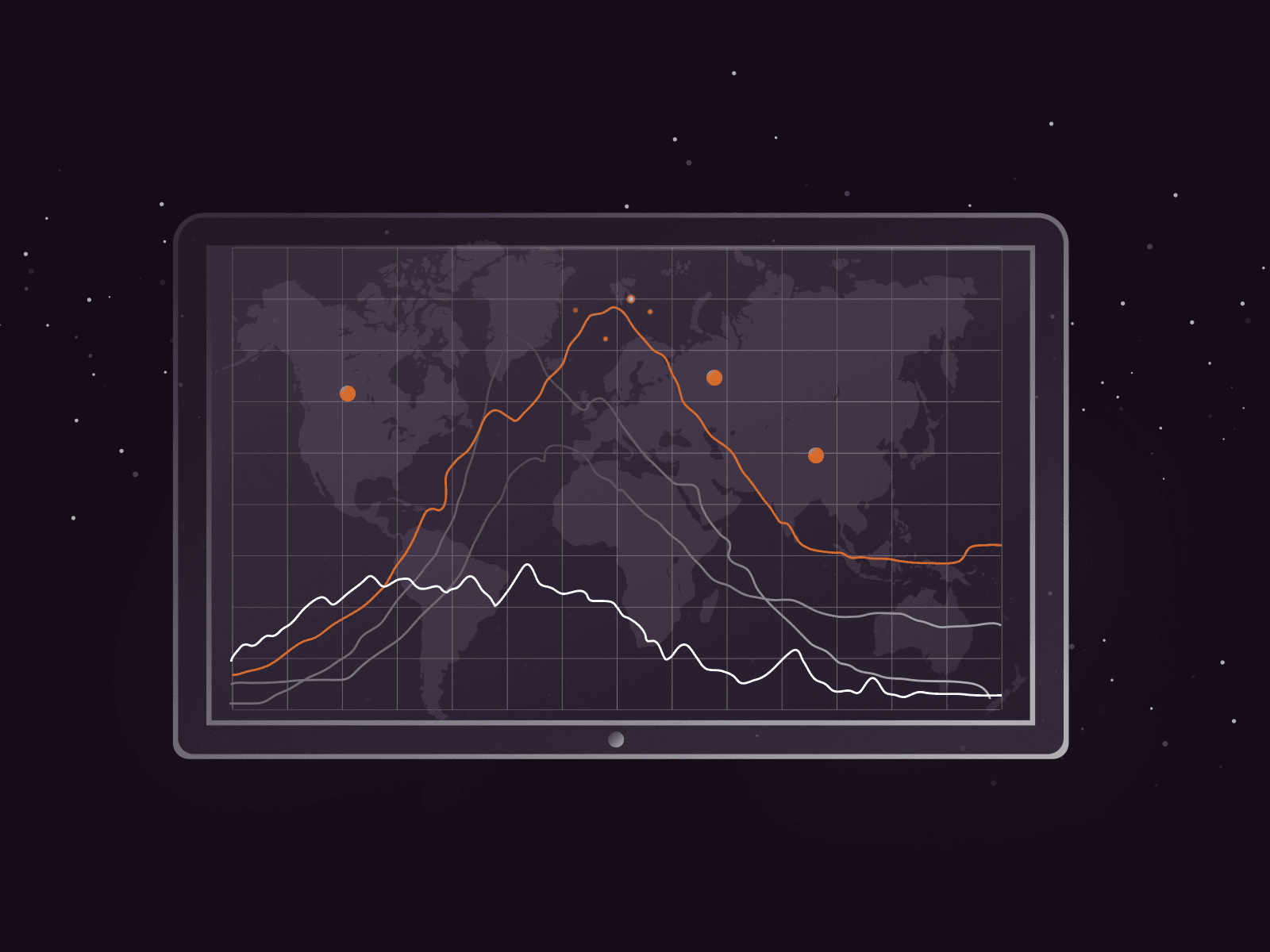
- Simultaneous graphs for PPS and BPS

How to Access Real-Time DDoS Protection Statistics
To access these metrics, simply go to your Gcore personal account > IaaS Protection > Reports > Traffic.
Key Features
Let’s check out the new features in more depth.
95th Percentile
The 95th percentile is a useful metric because it helps you understand the “normal” range of traffic variability on your network by filtering out short-term spikes. If the traffic unexpectedly exceeds the 95th percentile for an extended period, it may well indicate that a DDoS attack is happening. You can identify and react to this potential threat in real time.
Minimum and Maximum Values for Input Dropped and Passed Traffic
To effectively protect your network, it’s essential to know not only what’s passing through but also what’s being dropped. Real-time visibility into minimum and maximum values for input dropped and passed traffic helps you pinpoint areas of concern instantly. This granularity of data allows for more precise troubleshooting and mitigation.
The minimum value for dropped traffic should ideally be zero during normal network operation; in other words, no legitimate traffic should be dropped under normal circumstances. However, during a DDoS attack, the minimum value for dropped traffic may increase significantly, depending on the severity of the attack.
Simultaneous graphs for PPS and BPS
You can now view both packets per second (PPS) and bits per second (BPS) on the same screen, simultaneously. This makes it easier to correlate data and understand the bigger picture of your network’s traffic, including the nature and impact of a DDoS attack.
Conclusion
We remain committed to providing state-of-the-art DDoS protection services. With the introduction of real-time statistics, we’re empowering our customers with instant insights into their network security. We’re continuing to expand our product features to optimize network security.
Don’t wait until the next DDoS attack to take action. Try Gcore DDoS Protection for free today. Your network’s security deserves nothing less.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.