TCP DDoS (distributed denial-of-service) attacks pose a significant threat to network infrastructure. They exploit vulnerabilities in the TCP protocol to overwhelm servers and disrupt legitimate traffic. This article explains the mechanics of TCP DDoS attacks, their potential impact, and effective strategies for prevention and mitigation. We’ll explore different types of TCP DDoS attacks, such as SYN floods and ACK floods, and discuss how to safeguard your systems against these threats using techniques like SYN cookies, traffic filtering, and load balancing.
What Is a TCP DDoS Attack?
A TCP DDoS attack (Transmission Control Protocol distributed denial-of-service) is a type of cyberattack that targets the TCP protocol, a fundamental communication protocol used in networked systems. DDoS attacks aim to disrupt normal traffic on a network by overwhelming it with a flood of malicious traffic.
In a TCP DDoS attack, the attacker uses multiple compromised devices, often referred to as a botnet, to send a huge number of packets (small units of data) to a target network or server. The goal is to overload the network components, making them unable to handle legitimate requests from real users.

TCP is widely used for internet communications, including web browsing and email, but it wasn’t originally designed with robust security features. This lack of built-in security makes it vulnerable to exploitation. Hackers can send different types of TCP packets to execute their attacks. To understand this, let’s examine how TCP normally functions and what happens during a DDoS attack in the three most common TCP attack methods.
How Does a TCP DDoS Attack Work?
When a device, like your computer, wants to connect to a server, such as a website, it follows a three-step process known as the TCP handshake.

Each type of TCP DDoS attack (SYN flood, SYN-ACK flood, and ACK flood) targets a different stage of this handshake. By overwhelming the server at each stage, the attacker disrupts the handshake process, causing downtime and service disruption for legitimate users.
Let’s look at how TCP works and how different types of attacks exploit each stage.
Initiating the Connection: SYN Flood
- Normal process: Your device sends a SYN packet to the server to request a connection.
- SYN flood attack: The attacker sends a massive number of SYN packets to the server, pretending to request connections. The server tries to respond to each request by sending SYN-ACK packets. However, since the attacker never completes the handshake, the server is left waiting with numerous half-open connections, consuming its resources and making it unable to handle legitimate requests.
In an SYN flood attack, the attacker can use their own resources to send the requests or use TCP/IP hijacking to spoof legitimate IP addresses, making the malicious requests appear genuine. The spoofed systems do not respond to the SYN-ACK packets because they are unaware of the SYN packets sent on their behalf. Even though the server eventually drops these half-open connections, the sheer volume can exceed the server’s capacity, rendering it unresponsive to real clients.

Acknowledging the Request: SYN-ACK Flood
- Normal process: The server receives the SYN packet and responds with a SYN-ACK packet to acknowledge the connection request.
- SYN-ACK flood attack: The attacker sends a large number of SYN-ACK packets to the server without any corresponding SYN requests. The server has to process these unexpected packets, which uses up its resources and disrupts its ability to function properly.
A SYN-ACK flood leverages an unusual approach by sending SYN-ACK packets to the server. Even though they are not part of a legitimate handshake, these packets must be processed, and a significant number of such packets can cause server-side disruptions.
Completing the Handshake: ACK Packets
- Normal process: Your device responds to the server’s SYN-ACK packet with an ACK packet, completing the handshake and establishing the connection.
- ACK flood attack: The attacker sends a flood of ACK packets to the server. These packets look like legitimate responses, so the server spends its resources processing them. This overwhelms the server, making it difficult for it to handle actual connections from real users.
An ACK flood exploits the TCP function for data delivery acknowledgment. When a client receives the requested data, it sends an ACK message to inform the server that the data was successfully received. Attackers take advantage of this by sending a large number of forged ACK packets, which look identical to legitimate ones. This overwhelms the server, as it cannot distinguish between real and fake ACK messages, leading to resource exhaustion and service disruption.
What Damage Can a TCP DDoS Attack Cause?
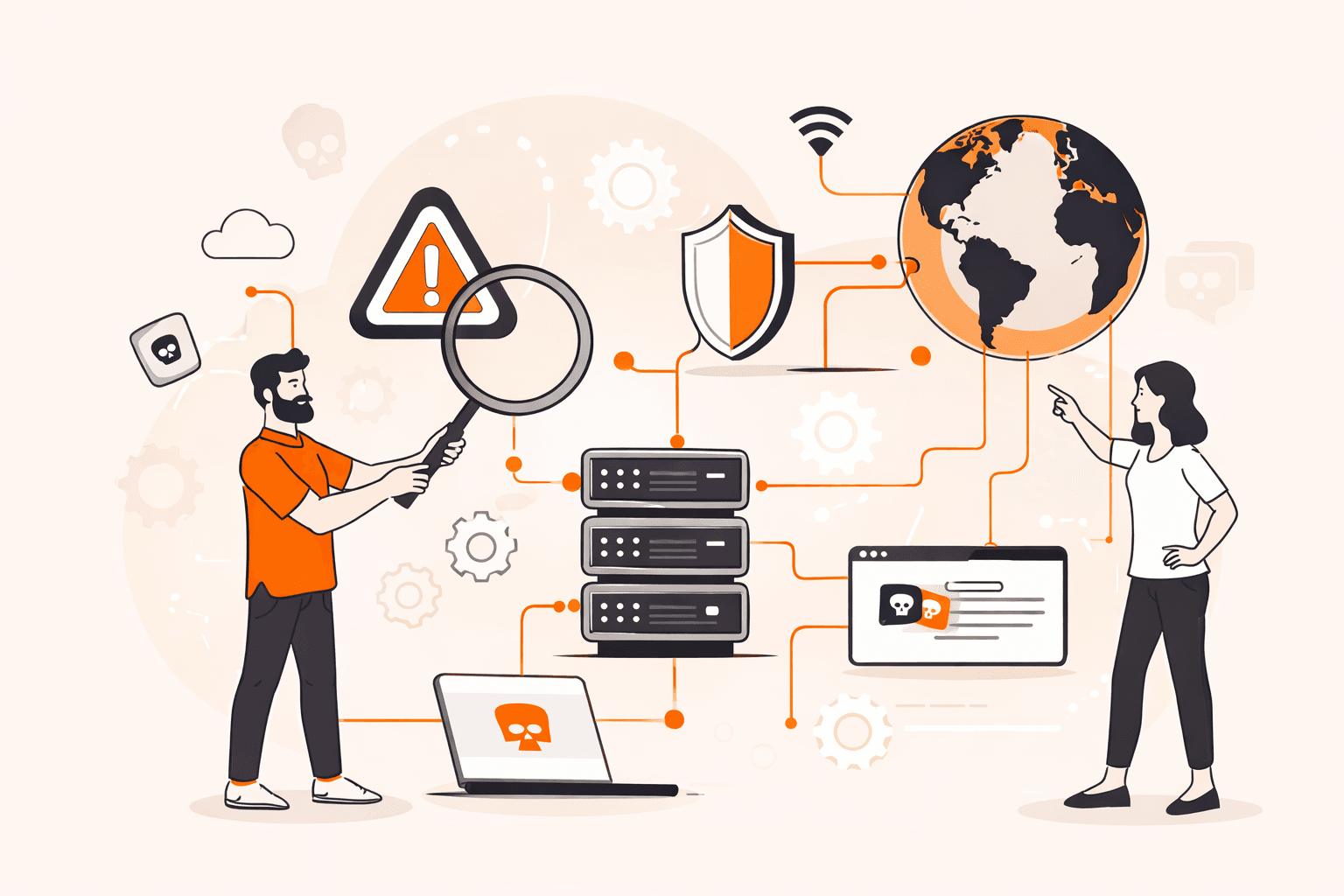
A successful TCP DDoS attack overwhelms the target server with fake requests, rendering the server unavailable to real users and the services relying on it. The duration of the downtime and the criticality of the affected services can result in significant financial losses and reputational damage for the business. Unprotected businesses lose an average of $6000 per minute during a DDoS attack. The unavailability of an online banking service or a medical institution can cause real distress and disruption with serious consequences for customers.
DDoS attacks can also act as a diversion for the target company’s IT and security teams, acting as a smokescreen for other malicious activities. While the incident response team is focused on restoring the attacked server’s performance, hackers might exploit the distraction to carry out phishing attempts or other attacks on sensitive information stored on the server.
How to Prevent TCP DDoS Attacks
When an attack succeeds, it’s already too late to prevent it. Therefore, the best tactics against all kinds of DDoS attacks are defensive measures.
One option is to use a comprehensive third-party DDoS mitigation service, like Gcore DDoS Protection, and leave it to the specialists. We recommend this approach, as using a robust, proven protection service is usually the most convenient and effective strategy.
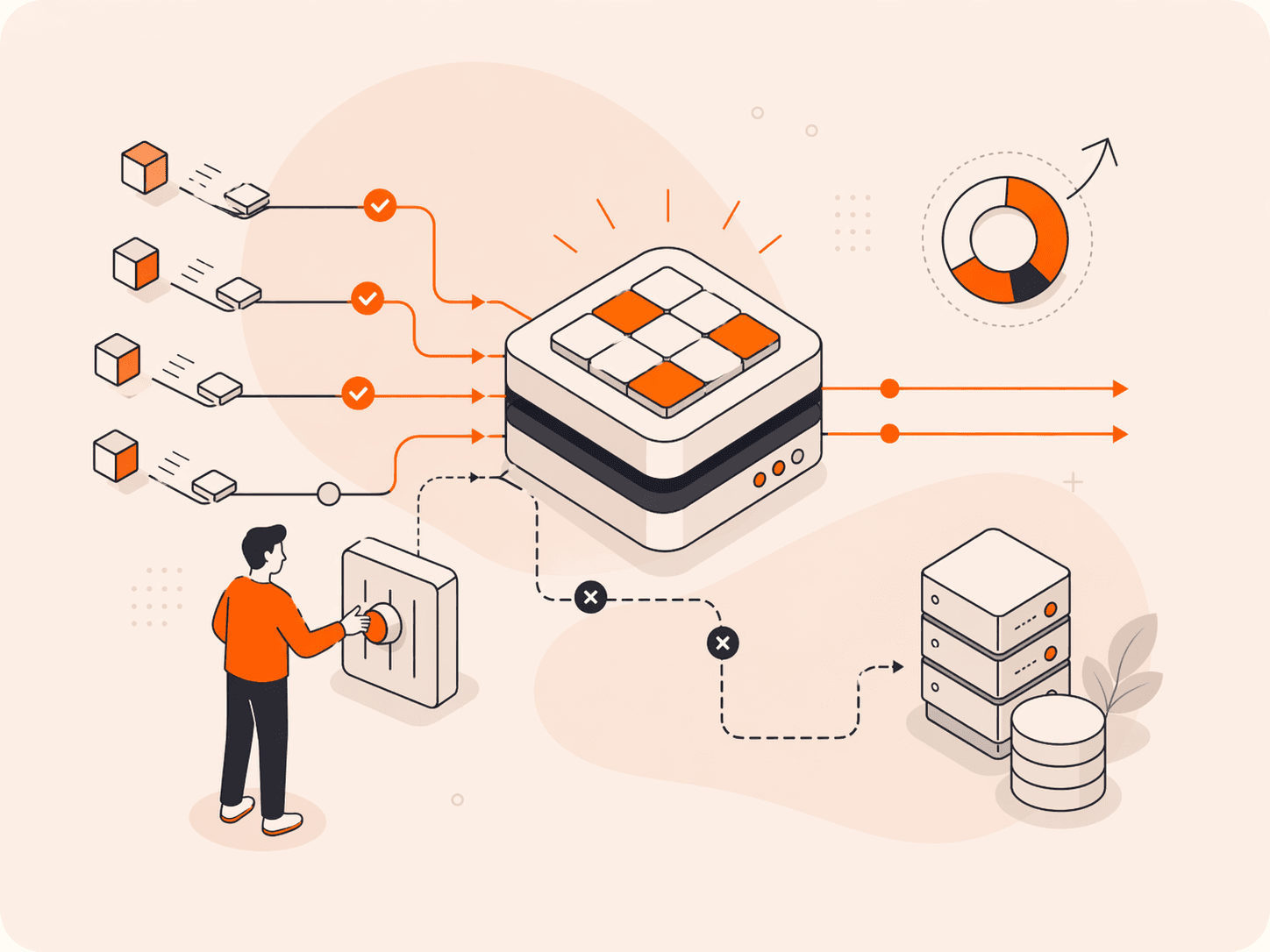
Alternatively, you can attempt to apply prevention mechanisms yourself. For TCP DDoS attacks, these include the following:
- SYN cookies: Protect against SYN flood attacks by adding a special value to SYN-ACK packets. The server will only restore the connection if this value is returned in the client’s ACK message, preventing half-open connections from consuming resources.
- Filtering and blocking: Identify and block traffic from irrelevant sources or patterns that seem suspicious.
- Blocking unused ports: Reduce the potential attack surface by closing ports that aren’t in use.
- Rate limiting: To prevent overload, set thresholds for the amount of traffic the server can handle, including the number of SYN requests.
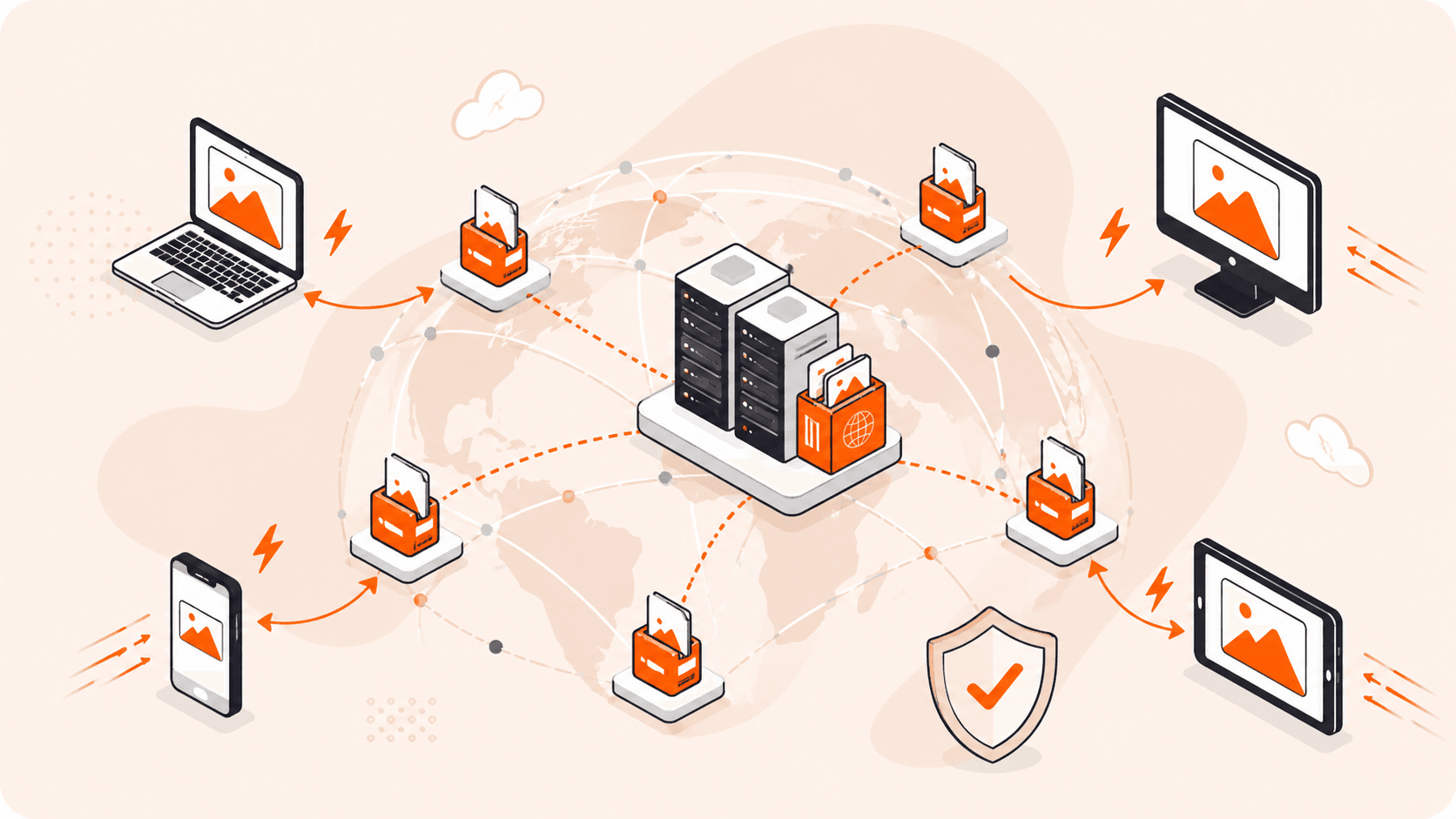
- Load balancing and redundancy: Distribute traffic using load balancers and have backup servers ready to handle increased traffic volumes.
- Caching and CDNs: Use caching and content delivery networks to minimize the resources needed to handle repetitive requests.
However, following best security practices doesn’t eliminate the risk of an attack entirely, so it’s also important to monitor traffic for spikes and analyze such spikes for anomalies in order to react promptly in case of an attack. If you’re undertaking DDoS mitigation yourself, this will involve some manual processes. Third-party providers will analyze traffic on your behalf, and some, like Gcore, offer real-time visibility into traffic so you can watch DDoS attacks being stopped as they happen.
Thwart Attackers with Gcore DDoS Protection
Our global network of scrubbing centers is engineered to keep your business operational during a DDoS attack. Your customers will experience uninterrupted functionality even during a DDoS attack, no matter the type. Gcore scrubbing centers are equipped with backup copies of critical systems and network equipment, underscoring our dedication to providing continuous service and robust security.
Gcore DDoS Protection offers businesses the following benefits:
- Robust infrastructure: With over 148 Tbps of network capacity and a global network that’s constantly learning from millions of internet properties, Gcore protects you against the largest and most sophisticated attacks.
- Proprietary DDoS protection solution: Tailored specifically to ward off a broad spectrum of DDoS threats.
- Detection of low-frequency attacks from the first query: Even the most subtle attacks are detected.
- Exceptionally low false-positive rate (less than 0.01%): Maintains normal operations by accurately distinguishing between legitimate traffic and attack vectors.
- Real-time statistics in the control panel: Offers immediate insights into traffic patterns and potential threats, allowing for swift action.
- Server protection in your data center: Extends Gcore’s protective measures directly to your infrastructure through a Generic Routing Encapsulation (GRE) tunneling protocol, regardless of location.
- 24/7, highly qualified technical support: Ensures that expert help is always on hand, day or night, to address any concerns or attacks.
- Exceptional uptime rate with 99.99% SLA: A seamless and uninterrupted user experience backed up by Tier III and IV data centers.
Conclusion
DDoS attacks, including various kinds of TCP attacks, are still a real threat to online services and can cause real damage to businesses. Preparing for the attacks in advance, however, can help to mitigate their consequences or avoid losses completely.
Experience the peace of mind that comes with advanced protection with Gcore DDoS Protection for comprehensive security against DDoS attacks. With over 1 Tbps of total filtering capacity and a 99.99% SLA, your digital assets remain protected from even the most complex, sophisticated, and sustained attacks. Gcore helps to maintain the continuity of your online services, regardless of potential attackers’ motivations.
Related articles
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.